USER MANUAL XNP6120H Hanwha
NAS - INDICATIONS DU FABRICANT
the following IP address:
Configuration HLC (Highlight Compensation)
InstallInstaller/retiree le certificat.
2. Cliques sur
3. Sélectionnez ou non .
4. Le tableau représenté le degré de falsification.
Réglez la sensibilité au niveau de faisification à défecter (page: 1 à 100).
5. Reglez la sensibilité
Plus la valeur regiele est elevee, plus la rection de la camera est sensioile (page: 1 à 100).
6. Specifie theDurée minimale de surveillance.
Un signal d'évenement est géné si un état supérieur au
niveau de détction resté pour la durée minimale de surveillance (unité : secondes)
7. Indiquez s'il faut excure les zones sombres
Cette fonction rençée de désigner les zones sombres duu au déscéarci-dessement de l'obscurité étant bloqué par un objet. En dépôt de cette propriété, si vous souhaïez excure une alarme pour ces changements brusques de la luminosité de l'éclair telisque que le déscéarçage, vous devazé activier cette fonction.
8. Choisissez d'utiliser ou non le transfert intercellulaire.
9. Configu que le calendrier de mouvement de I'evenement et les conditions de mouvement de I'evenement.
Poe otieni de plus animes informations sur les option confing, action even. et Heure d'activation reportez c la section Entrae 102
10. Une fois que vous aze effecte ceci, cliquez sur [Appliqueur]
1 la détention sera réconnue après stabilisation pendant une cortaire période de temps (environ 5 secondes). Pendant la stabilisation, la détction n'est pas disponible.
S de fausses aimes sont frquement generees, dmuez gratuellement la sensibilite pour minimiser les fausses aimes.
S you uis s t e e e e e e e e e e e e e e e e e e e e e e e e e e e e e e e e e e e e e e e e e e e e e e e e e e e e
mais une détction enconnue peut se produit en response aux changements d'objets en mouvement ou de luminosité
Dans les cas suivants, la force de détction de falsification peut etre defectueuse.
Environnement de surveillance avec fond simple, nut et environnement de faible niveau lumineux.
-Vibrations severes de la camera ou changements soudains d'éclairage
Détction de brouillard
Voupez configurer les parametres pour generer un signal d'evénement lorsque du brouillard est detecté.
1. Depuis le menu Configuration, selectionnez l'onglet
2. Cliquez sur .
3. Sélectionnez ou non :
4. Configures parametres de chaque element
- Niveau de détction: une alimentre est générale si le niveau actual est supérieur au niveau de détction configuré.
- Sensibilité : plus l'intensité est élevée, plus le graphique de niveau supérieur est produit pour la même catégorie.
Durée minimum (s) : une alarmed est généree si I'elal de

5. Configures le calendrier de mouvement de l'évenement et les conditions de mouvement de l'évenement.
Defog: Sponsifies whether to use the fog removal function when fog is detected.
Pour otderin de plus amiques intemations sur les options et reportez-vous a la section « Enetrée d'alerte (page 52)
6. Une fois que vous ayez effectué ci, cliquez sur [Applique].
Ares qu une alarme pour la detction de brouillard est generne, s you voulez receive une alarme pour la detction de brouillard a nouveau, vous devang roscir a un stat stable au moins une fois. L'amérisation video après le crash au brouillard n'est pas risquecomme non un stat stabilo. Les exerclles du rottur a un stat stabil sont les suilvants.
La case a cacher Detction de broillard est disactio
La wioe est inerterfiable car le brouillard ou la fumede disparait.
Dans les cas suivants, les performances de detection du fou pouvaient et alles ou un dysfonctionnement pouvait survenir.
Environnement de contrôle monotoné, environnement nocturne ou à faible éclairage
Changements soudains de l'ocailage (par exceme l'extinction de la lumiere interneure)
-Objectif blocué par un object large qui couche la quasi-totalité de l'ocan
-Modifie I'oplet cble en changant la position de la camera.
Detection de visage
You can configure the settings to generate an event signal in response to the detection of a face in the specified area.
1. Decoui le menu Configuration, selectionnez Ionglet
3. Sélectionnez ou non .
4.Défiinissoz uneat.
Zone d'intérêt, ce signal d'évennement peut se produit au tableau est detecté dans une zone ou un polynogoit est configuré.
Zone exclue: le signal d'évenement peut se produit si un visage est detecté à l'exercice de la zone où un polygone est confugué.

5. Réglez le niveau de sensibilité.
+ Plus la sensibility est cieve, plus la detction des visages est distilie at preise.
6. Si vous utilise «Espace dynamique basé sur les mouvements», la position et la tallie de la zone ROI sont automatiquement ajustées en fonction de l'endetroit où le mouvement s'est produit sur l'écran de surveillance.
7. Configurez le calendrier de mouvement de I'evénement et les conditions de mouvement de I'evénement.
Pour octobre de plus anlles informations sur les crlions et , reportez you a la section Entrée d'alerte (page 52)
8. Une fois que vous ayez effectué caci, cliquez sur [Appliquer].
Dans les cas suivants, les performances de detection do visque peuvent ettre altredas ou un dysfonctionnement pouc so produire.
L'angle ou l'inclinaison du visage est different de la direction d'imagerie (par exemple, appui renversé)
La personne porte des accessoires qui couvrent le visage tols que des lunettes, des lunettes de soioli, un chapeau ou un mousse.
Le visage est fou car la camera n'est pas mise au point
Durant la nut ou dans un environnement a faible luminance
La luminosite du visage est anormale en raison de la direction d'elastirage, comme le retrodelairege
écran de configuration
IVA (analyse videoe intelligente)
Vouvez coupez configurer les parametres pour générer un signal d'éveniment lorsqu'un mouvement ou une situationipoprondant au niveau d'éveniment的专业isé, net d'actifs.
1. Depuis le menu Configuration, selectionnez l'onglet
2. Clique sur
3. Sélectionnez ou non
4. Configurar les régles à détaquer. Pour plus d'informations sur les paramétres, reportez-vous à la section "Configurer les régles d'analyse". Les régles configurable sont les suivantes.
- Passage: vous pouvè défector un objet passant dans la direction selectionner une ligne virtuelle spécifique.
Intrusion : vous pouvez détector l'émergence d'un objet en mouvement dans une zone virtuelle.
- Saisir: detecte un objet entrant de l'extérieur vers l'intérieur de la zone virtuelle.
Sortie: Detects an object exiting from the inside to the outside of the virtual area.
- Apparition (Disparition): déetecte un nouvel object apparaissant dans une zone virtuelle, qui est surveillee pendant une période de temps espacifiée après que sa position soit fixe, ou défacto un object fixe qui disparait et n'est pas surveillance pour la durée de surveillance.
Flanero: obstruct a objet cront a l'interneur de la zone virtuelle pendant plus longcomps que la durée de surveillance.
5. Choisessez d'utiliser ou non le transfert intercellulaire.
6. Selectionnez les zones que vous ne souhaitez pas inclure dans l'analyse et les zones exclues.
7. Regléz le niveau de sensibilité et la taille d'intérêt (si nécessaire). Pour plus d'informations sur les paramétres, reportez-vous à la section "Paramétres commun".
8. Configures the calendar de mouvement de l'évennement et les conditions de mouvement de l'évennement. Pour anter de plus amples informations sur les options et reportez sous la section (page 52)
9. Une fois que vous avez effectue ce qui cliquez sur [Appliqueur].

Vouypouez configurer des regles d'analyse individuelles comme suit.
Passage
1. Selectionnez Fonglet
2. Cliquez avec le bouton gauche de la souris sur l'ecoran pour spécifier le début et la fin de la ligne à la position désirable à détector.
3. Selectionnez une direction d'intérêt
4. Une fois que vous aze effectue cec, cliquez sur [Applique].
5. Pourumper les regles configures, cliquez avec le bouton droit de la souris sur la ligne et cliquez sur la bouton [OK] dans la fenetreertextuelle qui appealait:
Intrusion, Saisir, Sortie, Apparition (Disparition), Flanerle
Cliquez sur l'englet
2. Une zone peut supporter un polygons ayant jusqu'à 8 sommets. Àprous avoir créé un polygons en selectionnant 4 sommets sur l'image, sélectionné chaque ligne du polygons déjà fabriqué et vous pouvez ajouter jusqu'à 4 sommets supplémentaires pour creer le polygons souhaite.
3. Dans la zone virtuelle configuee, selectionnez une categorie d'analyse.
4. Une fois que vous ayez effectué ceci, cliquez sur [Appliqueur].
5. Pour suprimer les régles configures, cliquez avec le bouton droit de la scuris sur la ligne et cliquez sur le bouton OK dans la finière contextuelle qui apparait.
Paramètres communs
Les régliages commons sont des régîages pour augmenter la precision de détction et minimier les faux positifs, en fonction de l'environnement d'utilisation.
Sensibilité
1. SéLECTIONNZ'onglet
Vous pouvez modifier la sensibilite de disition de fond d'ecran des mouvement.
Dans une situation ou les objets peuvent ettre ciearement disiglles aenei plans, regleu sur un nivea de sensiblile faible. Pour le solonar oposse, dans quel il est diffieile de distingue des objets, comme dans une situation d'acquire faible, regleu a un nivea elevé
2. Une fois que vous avez effectue cecl, cliquez sur [Appliquer].
- Taille
1. Sélectionnez l'onglet
2. Pour chaque rectige qui relate le taillie minimale et la taillie maxime, ciquez droit sur le sommet en bas a dioir pour lo decaoir o te codimensionner.
Les mouvements inférieurs à la salle minimale spécielle ou supérieurs à la salle maximaile ne sont pas dédictés. Pour éffecter les déférences involutantes causées par de grande et一个小bouts, définièez les dimensions de mouvement minimum / maximum appropriées en fonction de toute environnement. Né que les mêmes mouvements sur le meïme emplacement peuvent être dédictés différément selon leur saule de détction; il est recommendé d'émisser et d'indure la différence tolerable lors de la definition des tailes de détention minimale / maximaile.
3. Une folis que vous avez effectue cecl, cliquez sur [Appliquer].
Suivi automatique
Il est possible de définir l'opération de suivi automatique en fonction de l'environnement d'installation et de générer un signal d'évitissement lorsqu'une caméra exécutée l'opération de suivi automatique.
1. Sélectionnez l'langit sur le menu Configuration.
2. Cliquez sur
3. Réglez le comportement du SUV uromatique de laamera . Hauteur de laamera : regler la hauteur de laamera.
I réglage linéxact de la hauteur peut diminuer la fonction de suivi (hauteur: 2,5m ~ 30m)
- Zoom : vous pouce utiliser la fonction d'intéropabilité du zoom avec le comptement de suivi automatique.
- Maintenir la ballie de la cible : « vous pouverez régier la limite de zoom avant de la visée lorsqu'vous scétonné la fonction d'intérêpérabilité du zoom avec le comportement de lui automatique.
- Affiche t'éternin: le t'éternin indiquant la cible du suivi est affiché sur l'écran.
Zone excise :的选择题不该以d'activation du domaine qui a été définir. Pour définié le domaine, reportez-vous à 'Pour désigné le domaine', (page 57)
Outiler automatique : le suivi automatique fonctionne sans restriction de durée . Si l'objet visé disparait du champ , laamera restée à sa position en attendant l'objet et redémande le suivi si l'objet reapparait .

4. Configurez le calendrier de mouvement de I'evénement et les conditions de mouvement de I'evénement.
Pour avoir de plus simples informations sur les options et , reportez-vous à la section «Entrez d'alerta», page 52:
5. Une fois que vous avez effectué caci, cliquez sur [Appliquer].
Pour définiir le domaine
Dans le domaine désigné, le suivi automatique ne démonte plus même lorsque des mouvements sont dédictés. Jusqu'à 3 prêtiages peuvent être enregistrées pour le paramétrage de domaine.
1. Maintenez la souris ciquee sur l'imag et faies-la glisser pour regler la zone souhaitee
2. Saisissez le nom, puis cliquez sur [OK].

Le Domaine definite ne s'arrete pas de suive meme l'objet de suivi se deplace dans le Domaine.
Dans les conditions suvantes, le suivant automatique fonctionne normalement.
Roglerhauteur:Au minnimum 2,5 m ou plus,Jusqu'a 30 m oins
-Rogier type: Tpe intrieur a nveau stabilise sans indineon ou extrieur monte au plafond
Objet suiv: Une personne entrain de marcher et se déplacant sur le pian horizontal (Hauteur approximative 170 cm)
écran de configuration

Elle pot etre dans l'imposibilite de suire une cble ou entrainer des dysfonctionnements dans les situations suivantes.
-En Presence de multipes ojeits so d'oplacant dans la zone de capture
Lorsqu'ele est caché ou masquè par d'autres objets ou Installations mobles
enl absence d'une legere differenc entre foelse deplacant et lariere-plan
JIn objet: trop pett ou trop grand
Lorsqu'unbject se depace trop rapdement ou trop lentement
Lorsqu'un objet en mouvement passe juste en dessous de la camera installee
Lorsque la trojecte d'un objet en mouvement ne correspond pas à la hauteur du sol installée à titre de reference
-Mauvais tempos tel ou un vent violent de la reige et de la plue
Lorsque la zone de capture est nombre
-En presenoe de brusques variaions de luminosite
-En presence d'un flash de lumiere dirige vers la camera ou la zone de capture
-En presenza d'une lumière ou d'une reflexion de lumière dingée vers la camera
Lorsque la video trenble suite a des secousses de la camera
Lorsque e couerle de la lentille et la couerole du gradateur sont tines ou moulles
-En presenca d'un changement d'ae de la camera
Detection audio
Permet de détector le son dépassant le niveau spécifique et de déclencher un événement en conséquence.
1. Dequis le menu Configuration, selectionnez Ionglet
2. Cliquez sur
3. SéLECTIONnez ou non .
4. Récipes le niveau de son de la détéction audio
Plus le niveau est bas, moins le changement de son est détecté.
Lo riveau de detction auo est cnoqu par normalise les donnnes d'entre la une valeur comprise entre 1 et 100 et qui derise le signe plus granque que ie riveau de seuil. Il est pas le au riveau de chevdels id6

5. Configurez le calendrier de mouvement de I'evénement et les conditions de mouvement de I'evénement.
Pour oie n de plus anles informations sur les collins et . reportez-vous a la section Entrée d'alerte (1942)
6. Une fois que vous ayez effectué cecl, cliquez sur [Appliqueur].
Sclcricn-Video&Audio--Audio Configuration>etregne la volume apprope pour voire microponee comme sur aerere audio, la seule ne la location de ralign:audio plus longeur comporelles.
Si le niveau audio detecté est trop cas, reglez ie gain d'entree audio a un niveau plus eleve dans .
Vouss potier utisir la fonction de detction audio lorsque la camera est connecte a un peripienque d'entree audio.
Classification sonore
Voussouspouce configurer les parametres pour generer un signal d'évenement en réponse à la détction d'une source sonore specifique.
1. Depuis le menu Configuration, selectionnerz?onglet :
3. Sélectionnéz ou non .
4. Régrez le niveau d'énergie audio de la source sonore à classer. La valeur du niveau d'énergie pour l'audio d'entrie est mise à jour periodiquement de droite à gauche, et est tirée sur la zone. La classification des sources sonores n'est approubable qu'à l'audio à un niveau supérieur à la valeur spécifiée.
5. Configurez les paramétres de chaque éléments
- Brui relduit: specifiez le statut
Si le bruit dans le milieu environnement est trop fort, depassant 55 a 60DE utilise la fonction de reduction du bruit. Si la fonction de reduction du bruit est utilisée, la fonction de classification du son peut être désignée ou poult functoriel mal en fonction de l'environnement, car la source socrne d'origine est réduite. Si vous utilise le titre de reduction de bruit dans un environnement silencieux, la fonction de classification des sources socrne peut être alliée.
- Catégories : selectionnez une source sonore à classer.
Definition de la source sonre. Son de crit brui eige generé par les humains, let qu un cti ou un hurlement par un adulte male / femelle ou des enants Son de coup de feu:son de dir exaclant les coupes de feu tirés rapidement et consecuils Son d'expoison:brui d'exposion soudaine qui est le résultat d'une action destructrice Son de verre brie:brui de bris de verre
6. Choisissez d'utiliser ou non le transfert intercellulaire,
7. Configuez le calandrier de mouvement de l'évennement et les conditions de mouvement de l'évennement. Pour oitenir de plus anlles informations sur les options et reportez-vous a la section «Entrez d'alerte « (page 52)
8. Une fois que vous azevea effectue ceci, ciquez sur [Appliquer].

- Dans « Video & Audio » « Paramétrés audio » 1 est recommendé de regler le gain d'entrée audio à une valeur comprise entre 4 et 6.
- Dans «Video + Audio» «Réglages audio», si vous regissé le source d'entrée audio sur un microphone externé, les caractéristiques recommendées pour un microphone sont les suviantes.
-Plape de frquence:40a16000Hz
Impedance:15009
Sensibility: -40 ± 3 dB (7.1 ~ 14.1 mV)
Dere les cas suive,les performances de la classification des secues socrn pas enotde ou mesteront des dyshtcnionmores. -Los sors de coup de fou sont genere consoutement comme le son product par une mitraleille poult que par un son a une unique origine.
Le buit est trop fort pour étre destingue de la source sone cible.
-2 sources sorores ou plus sont enretres simultanement
La classification de la source sonne est applice dans un environnement siendoué à la fonction de supression du bruit
-Un son d'appeulissements ou de cris se sait entender à une distance proche (à incins d'un métre) de la camera
- Unosourso sorso fortocn napertont a aucno des catogores de sourso sornot tellos que le son d'un avon ou d'une siere est saucraientment generated
Le microphone exter n'est pas conforme aux specifieations recommandees
CONFIGURATION DU SYSTÉME
1. Deux le menu Configuration, selectionnez l'englet [图]
2. Cliques sur Informations produit
3. Verifies the informations relatives à laamera ou fournissez les détails selon l'environnement réseau.
- Modèle: nom du modele du produit.
- Numéro de série : numéro de série du projet.
Nom de l'apcereil: Indiquez un nom de periphereque qui s'affchera sur Iecran Direct.
Emplacement:Permet de specifieI'emplacement de la camera a installer.
Description: Founissez les informations détaillées sur l'emplacement de la camera.
Note: Fournit une explication relative à la camera pour une meilleure compréhension.
Langue: Sélectionnez la langue de votre besoin pour l'affichage à l'écran de Web Viewer.

La langue par défaut est définie sur .

4. Une fois que vous ayez effectue ceci, cliquez sur [Appliquer].
Mise à niveau / redémarrage
1. Depuis le menu Configuration, seLECTIONnez l'onglet -Systeme (图) >
2. Cliquez sur
3. Sélectionnez chaque élément et réglez-le convençlement.
- Mise à niveau: Effectue la mise à niveau du système.
Lors de la reconnction, la visionnouse Web ne fonctionnera pas normalément si le cachet du navigateur n'est pas complètement nettoyé.
Paramétres par défaut : Rénéralisation toutes les informations de configuration, y comprise les réçignées de l'apparil aux paramétrés d'utilité. (Tourefels, les journaux ne sont pas reiniétables)
- Cochez la case et les paramétrés autres que les paramétrés réseau et les paramétries d'ouverture de la plate-forme seront réinitialisées.
Le systeme d'admission IP sera regie par default sur DHCIF si vous initiaitner la camara. Si aucuns servir DHCIF n est trouve, les régies precedents seront automatiquement restués.
- Configuration sauvegarde et restauration: Sauvegarde les réglages du système actuel avant d'effectuer un processus de restauration. Le système redénaire automatiquement après la sauvegarde ou la restauration.
- Redemarner: Redemarre le système.
écran de configuration
Pour réaliser une mise à niveau
1. Cliquez sur [Parcourir ( ) ] pour specifies un fichier a metre a niveau.
2. Cliquesur [Mise a niveau]
3. Une barre de progression "Mise à niveau" vous invite à indiquer l' état de la mise à niveau.
4. La mise a niveau terminée, le navigateur se ferme et laamera redemarre.
#
La procedre de mise a niveau peut necessiter un maximum de 10 minutes.
Si le proceessus de mise a niveau est intermoncu, la mise a niveau ne sera pas compltelement terminne.
Pendant le radimarag du systeme, le visionneur Web ne peut pas y accorder.
Vous poue telecharla verson la plus rercnte du product sur le site Internet de Hanwha Vision.
Pour sauvegarder les réglages actuels
1. Cliques sur [Sauvegarde].
2. Un fichier au format *.bin* est emerge du dans "Library" -> "Document" -> "Downloads".
Pour restaurer les reglages de sauvegarde
1. Pour restaurer les réglages de sauvégarde, cliquez sur [Restauration].
2. Sectionnez un fichier de sauvegarde de�ite choix.
Si you eflectue la savege de ou restauration, ne navigateur Web se ferner et la camera redemarera.
Si vous essayez de recuperer le chiffier de configuration sauvégand dans un autre méthode, certaines fonctions peuvent ne pas fonctionner correctement et vous devese changere régrée manuelle.
Journal
Vou pouvez consultier le journal système ou le journal des erreurs.
1. Depuis le menu Configuration, séctionnerlez'ordel [ ]
2. Cliques sur Journal
3. Selectionnez un type de journal.
Journal d'acces : Yous pouvez vérifier les informations dujournal qui contiennent les acces de l'utiliser et le tempsd'acces.
Journal du système: Vous pouvez consulter les journaux système dans lesquels sont consignées toutes les modifications du système, notamment les informations relay
Journal d'évén : Yous pouvez vérifier les journaux des événements, notamment pour les Informations relatives à l'heure.
4. Depuis laiste des journaux de droite, selectionnez un element a rechercher
S�� selecţionnez < Alt> dans le coin supérieur gauche de la lsté discuclante, tous les journaux correspondants au type de journal applicabilité seront affichés.
5. Si une page ne peut pas offérer l'ensemble des journaux disponibles, serviez-vous des boutons du bas pour passer à l'élément suivant ou revenir sur le precedé ou aller sur le dernier élément.
6. Cliquez sur le bouton Sauvegarde pour enregistrer toutes les données du jour dans le mode actuellement selectionnee dans la valeur dHorodatage create par la camera dans le fichter modemane-mode-camera.txt du dossier de telechangement du navigateur.
Chaque page afliche 15 journaux, le plus recent appeaissant en haut de laiste.
Chaque jour contien jusqu'a 1000 enreglements et après chaque 1000 enreglements, le jour le plus ancien est supprimé et un nouvel enrglement est généré.
Un utiliseur peut installer une application sur sa camera pour executer des tâches supplémentaires.
1. Depuis le menu Configuration, selectionne Ionglet Plateforme ouverte (O) >
2. Cliquez sur .
3. Cliquez sur le bouton [Parcouriel] pour selectionner le chiffre, cap dans le dossier de l'utilisateur.
4. Cliquez sur le bouton [Installer] pour Installer l'application.
5. Information de l'application Installée est affichée dans la liste.
- Désinstaller: Supprime les applications installées ou en cours d'exercice.
Application Go : Yous serez roirigés vers la page app. de chaque application.
Demarrage: Lance une application instalie.
- Arrêt: Interrompet une application en cours d'execution.
- Santé: Affiche les apolisations en cours d'écôuction, le taux d'occupation des ressources, le fil et le temps d'écôuction, etc.
- Priofo: Etablit la priorito des applications en cours d'execution.
Sépasse 80 %, l'arrêt d'une application en cours d'execution sera forcé. Dans ce cas, la priorité définie par l'utilisateur est utilisé pour déterminer quielle application devra être arrêté en premier.
- Démarriage auto : Lorsque l'allimentation ou les tâches principales de laamera sont actives, une
application pour laquelle l'execution automatique a ete activee demarrera automatiquement
Gestionnaire de tâches : Affiche le taux d'occupation des ressources d'une application en cours d'exercice dans voira camera
- Utilisation de la mémoire (%): Taux d'utilisation de la mémoire pour chaque application.
- Utilisation du CPU (%) : Taux d'utilisation de l'UG pour chaque application.
- Compte de processus: Nombre de processus créés pour chaque application.
Durée: Temps total d'exécution pour chaque application.
Tuer la tache: Fereune une application.
- Utilisation totale : Taux d'occupation total des ressources de la camera (incluant les tâches et applications principales).
S you avez des quostions a propos de l'utilisation ou l'installation, consultez te site web de Harwina Vision.

RÉSOLUTION DE PROBLEMES
PROBLÉME SOLUTION Lorsqu'un utilisateur de Windows 10 accédé à la visionneuse Web via Chrome ou Firefox, le volume sonore du microphone change périodiquement. • De qui se produit quand le pilote de microphone a été rédigé sur le pilote Realtek. Installez le péripérisque audio haute défiéction (pilote par défaut Windows) ou le pilote tiers comme pilote de microphone. Aucune video n'est affichée lors de l'accès libre au visualisateur Web de plug-in sur Safari via HTTPS. • Dans la fondre d'autorisation contextualle affichée lors de l'accès initiaI à https, cliqueur sur "Afficher certificat d'authentication" et sélectionnez l'options "Tousjours faise confiance lors de la connexion à l'adressé IP du visualisateur Web désigné". • Si le visualisateur Web ne peut toujours pas liètre une video après avoir sélectionné "Solvent" dans la failière de message ci-dessus, appuyez sur la touche de commande - Q pour quitter le navigateur Safari plus recommendé et suivez les procedures indiquées ci-dessus. Jo n'al pas accès à laamera à partir d'un navigateur Internet. • Verifier pour s'assurer que les paramétres de réseau de laamera sont appropriés. • Verifier pour assessor que tous les câtsos de rseau ont été correctement connectés. • Si elle est connectée en utilisant DHCP, vérifier que laamera peut acquérir des adresses IP dynamiques sans aucup problème. • Si laamera est connectée à un Rouleur large bande, vérifier que le renoi de port est configurié correctément. Le visionneur sa été déconnecté pendant le suivi. • Les visionneurs connectés se déconnecté à tout changement appporté à laamera ou aux configurations du réseau. • Verifier toutes les connexions de réseau. • Si laamera est connecté par un réseau PPPoe, il est possible que le visionneur sa déconnecté en raison de mauvaises conditions de réseau. Laamera connectée au réseau n'est pas déconnecté dans le programme Device Manager. • Désoilver les paramétres de pare-feu sur cette PC et chercher de nouveau laamera. Chevauchement d'images. • Verifier si une ou plusieurs cameras sont configurée à une adresse multidiffusion unique au lieu d'adresses différentes. Si une adresse unique est utilisée pour dos cameras multiples, les images peuvent se chevaucher. Aucune image n'apparait. • Si la méthode de transmission est configurée sur multidiffusion, vérifier si y a un roule qui prend en charge la multidiffusion dans le LAN sur lequel laamera est connectée.
PROBLEM SOLUTION La voix n'est pas enregistrree même si les parametres d'entree audio sont configurateurs. • Vous devez activer la case a cochier <Entree audio> dans <Basic> <Profil video>. <Détection mvt> de l'<Analyse> est régé sur <Activet>, mais je ne recoils pas de notification par e-mail même quand un événement d'analyse s'est produit. • Vérifier les réglages selon la sequence suivante: A. Vérifier les réglages <Date et heures>: B. L'option <Détection mvt> doit être régée sur <Activet>: C. Vérifier si l'options <E-mail> au menu <Config. éven> est cochée avant'utilisation. Aucun signal n'est déetecté au port Emission d'alerte, même en cas de génération d'un événement d'analyse videoi intelligente. • Vérifier les réglages de port de sortie de l'alarme. Impossiblè d'effectuer un enregistrement sur la carte mémoire Micro SD. • Vérifier que la carte mémoire n'est pas dééclueuse. La carte mémoire Micro SD est insérée mais laamera ne fonctionne pas correctement. • Vérifier si la carte mémoire est insérée dans le bon sens. Le fonctionnement des cartes mémoire formées sur d'autres apparçals n'est pas garantie sur cetteamera.
• Form活着 la carte mémoire à nouveau sous le menu <Configuration> → <Événancement> → <Stockage> Impossiblè d'enregistre sur le système NAS. • Assurez-vous que l'information enregistrée dans le système NAS soit correcte. Un rapport mentionné que le réglage du système NAS a echoué. • L'adresso IP du NAS est valide.
• D'irrotat ce passée du NAS est valide.
• Assurez-vous de pouvoir acceder au dossier désigné comme dossier principal en utilisant le ID du NAS.
• Les italics SMB/CIFS du NAS ne sont pas cachés.
• L'adresse IP du NAS et celle de laamera ont le même format. Ex: La valeur initiale du masque de sous-réseau du NAS et de laamera est 255,255,255.0. Si l'adresse IP est 192,168,20,32, alors l'adresso IP du NAS pourrait être celui qu'il part dans 192,168,20,1-192,168,20,255.
• Vérifier si vous avez tenta d'y acceder sous un autre nom d'utiliser sans formater le principal dossier utilisé ou saugardé.
• Assurez vous d'avoir utilisé l'equipment NAS recommendé.
OPEN SOURCE ANNUNCEMENT
GPL/LGPL software license
The software included in this product contains copyrighted software that is licensed under the GPL-CC BY. You may obtain the complete Corresponding Source code from us for a period of three years after our last submission of this product by sending email to http://cbvivikharwaha.com
If you want to obtain the complete Corresponding Source code in this physical medium such as G. HOMK, the cost of physically performing source dissection might be charged.
GPL SW
Component Name License URL
Bass Kornel GPL 2.0 Busesco GPL 2.0 http://www.busesco.net/downloads/annotation iprodust-4.3.0 GPL 2.0 ilabrix-1.4.21 GPL 2.0 http://tip.net.nl/other/projects othical 4.7 GPL 2.0 msr1-5.2 GPL 2.0 http://fco.intraked.org/pub/intro-site mi-dag-2.11 GPL 2.0 rs-sparse-2.11 GPL 2.0 http://www.rso.org/sparse/index.php? wpe_supplicant 2.0 GPL 2.0 bch-4.3.20 GPL 3.0 zomocmt GPL 2.0
LGPL SW
Component Name License URI
git Inc 1.041 2.0 Intel Corporation LGFL 3.0 reason-0286 LGFL 2.0 http://www.volant.org/height/
GNU GENERAL PUBLIC LICENSE
Version 2, June 1951
Copyright © 1998, 1997 Free Software Foundation, Inc. S1 Franklin Street/Filth Floor, Boston, MA 02110-1301, USA
Eeyone a prrnns to copy and dtrate wthtna copies of this lncase document, but changing it is not alioed.
Preamble
The Licensee for most software are designed to take away your freedom in share and change it. By contrast, the GNU General Public License is intended to guarantee your freedom to share and change from software. To make sure this software is fair for all its users, this General Public License applies to most of the Free Software Foundation's software and to any other program whose authors commit to using it. (Some other Free Software Foundation software is covered by the GNU Licensee General Licensee instead.) You can apply it to your programs, too. When we speak of free software, we are referring to freedom, not copyright. The free software platform that you use to build this application is a free version of the free version of this application. You cannot assign or modify it to another application without giving the right. If you want to know which application to install, you must use the free source code and give it back if you want it, that you can change the software or use choices of it in future versions...and then you know you can do these things.
To protect your rights, we need to make restrictions that forbid anyone to deny you these rights or to ask you to suture the rights. These restrictions can translate to certain responsibilities for you if you distribute copies of the software, or if you modify it.
For example, if you distribute copies of such a program, whether grants or loans you must give the recipients all the rights that you have.
You must missuse that they,too receive or can get the source code.And you must show them there leters so they know their rights.Werect your right with two stars.
Copyright the software, and Pifiof you his oce hich giv you logi porm to copy dtrus and/or modify the software. Also, for each authors protection and ours we want to make certain that everyone understands that there is no warranty for this free software. If the software is modified by someone else and passed on to us, we send it to the users to know what they have s not the original, so that any problems introduced by others will not reflect on the original authors' inputions.
i t i t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t f
TERMS AND CONDITIONS FOR COPYING, DISTRIBUTION AND MODIFICATION
Vssio 2, June 1981. Copyright © 1983, Inc. Series Software Foundation, Inc.
0. This License applies to any program or other work which contains a motion placed by the copyright holder, saying it may be distributed under the terms of this General License.
e "Program," please, refers to only such program or work, and a "Work session on the Program" means either the "Program" or any derivative work under copyright law; that is to say, a work containing the "Program" or a portion of it, either verbal or with modifications and/or translated into another language.
Activities cover than occurring distribution and modification are not covered by this License. They are subsidies to escape. The act of running the Program is not confidential, and the output from the Program is covered by this license which constitutes a world based on the Program's predecessor or having been made by the Program.
1. You may copy and distribute verbatim copies of the Program's source code as you need it, in any medium, provided that you conspcctusuy an
apprnepent poun on ech copny an approctible copny hne and dianl of wannry. keep in a the roce siter to this License and to the
You may change the price of the products or services you buy. And you may offer a free or low-cost service.
2. You may modify your copy or copies of this Program or any portion of it, thus forming a basis based on the Program, and copy and distribute such modified or copy under the terms of Section 1015 above, provided that you pay an initial all of these payments:
a You must cause the modified ties to carry prominent notices stating that you charged the fees and the date of any change.
e You must cause any work that you distribute or publish, in whole or in part contains or is derived from the Program or any care thereof, to be licensed as a whole at no charge to all third parties under the terms of this License.
In the modified program normally reads commands interactively when run, you must cause i., when started running for such interactive use in the most commonly used to point or display an announcement including an announcement statement and a notice that there is no warranty for this version.
you provide a warranty and that users may redistribute the program under these conditions, and taling the user how to view a copy of this License.
Exceclion The Program itself is InteRactive but does not formily print such an annoumertion, your work based on the Program is not required to print an annoumertion.
These requirements apply to the modified work as a whole. If identifiable sections of this work are not derived from the Program, and can be reasonably considered inappropriately and susceptible works in themselves, then this cannot, and its terms, do not apply to those sections when you can distribute them an appropriate work. But when you distribute the same sections as part of a whole which is a work based on the Program, the distribution of the whole must be on the terms of the Licensee, whose permissions for other licensees extend to the entire whole, and thus to each and every part regardless of who owns it.
Thus, it is not the intent of this section to claim rights or contest your right to work written entirely by you; rather, the intent is to exercise the right to control the distribution of derivatives or collective works based on the Program. In addition, mere aggregation of another work not based on the Program with the Program
for with a work based on the Prognostion a volume of storge or distribution medium does not bring the other work under the scope of this License. 3 You may copy and distribute to the above as a work based on it, under Section "Open access or reuse" in terms of the terms of Sections I and II.
above provided that you also do one of the following:
a) Acompanyy it with the complcx corresponding machines reacible source code, which must be distributed under the terms of Section 1 and 2 above on a medium customarily used for software interchange, or.
(a) Apply it with a written offer, paid for at least three times, to give any third party, for a charge no more, then your cost of physically performing source code is reduced by 10% of the remaining source code, or be distributed, near the terms of Section 1.1 and above on a modified customarily used for software interchange.
6) Anyon it with the intemaiion you received as to this offer to distribute, source code. This attern is allowed only for noncommla distribution and only if you receive a program in object code or executable form with such an offer. In accordance with Subseriab above). The source code of a work must present the printed form of the work, or making modifications (e.g., for an executable), complete source code (or all source code for all executees) copies, plus any organized written files. Plus, the sources must contain instructions and declarations of the executable. Otherwise,
as a specia cexeption, the source code detiruted need not indude anything that is normally distributed in either source or binary form with the major
component's component, kernel, and so on of the non-stricting system of which the execution runs, unless that component's functions accomplish the execution. A distribution of execution or object code is made by offering access to copy from a given group, then offering equivalent access to copy the source code from the same place counts as distribution of the source code, even though third parties are not compiled in copy the source along with the object code.
4. You may not copy, manipulate, or distribute the Trojan script as expressly provided under this License. Any attempt to otherwise to copy, modify,�藏 or distribute the Trojan script is said, and will automatically return your rights under this license.
However, parties who have received copies, or rights, from you under this License will not have their license terminated along such parties remain in full compliance.
5. You are not required to accept this license; show you have not agreed. However, nothing else grants you permission to modify or distribute the Program or its derivative works.
These actions are prohibited by law if you do not accept the Licensee. Therefore, by modifying and substituting the Program for any work based on the Program, you indicate your acceptance of the License to do so, and all its contents and such one for copying, distributing or modifying the Program or otherwise based on it.
6. Each time you receive buts the Program or any work based on the Programs, the student automatically receives a loose from the original lnsigner to copy. The student may also send the program to a friend or colleague and ask them to complete further refectioes on the explants' awareness of the right answer. Here, you are not responsible for eronging correspondence by third parties to this llustrus.
7. If, as a consequence of a court judgment or allegation of talent, misrepresent or any other reason not limited to issuer (issue), conditions are imposed on you (whether by court order, agreement or otherwise) that contradicts the conditions of this License, they do not excuse you from the conditions of the License if you cannot disclaim the so as to satisfy simultaneously your obligations under the License and any other pertinent obligations, item 1 as a consequence you may not distribute the Program at all.
I or example, it a patient license would not permit residency not distribution of the Program by all those who want to copy diversity or directly through you, thenre only way you would routinely own and this series would not to refrain entirely from distribution of the Program.
If any portion of this section is held over or unforced under any particular circumstance, the balance of the section is inverted to apply and the section as a whole is inverted to apply in either circumstance. It is not the purpose of this section to introduce you to marry any parents or other property right claims or to control validity of any such claims. This section has no specific purpose or preventing the integrity of the non-software distribution system, which is implemented by public license creators. Many people have made generous contributions to one of the wide range of software distributed through this system in reliance on consistent application of this system; it is up to the publisher/director to decide if she is willing to distribute software through any other system and a licensed cannot impose that choice. This section is intended to make homing down what is said to be a consequence of the text or this journal.
8. If the citation under use of the Program is not stated in certain countries either by persons or by copyrighted Interests, the original copyright holder who owns the copyright may be a member of the International Copyright Organisation (ILO) and/or the International Trade Marks Organisation (ITMO). The citation is a person only if no strong country has not this excluded. In such case, this course incorporates the Initiation as it refers in the body of its scope.
9. The Free Software Foundation may submit revised and/or new versions of the genera Public License from time to time. Such new versions of this similar spirit in this present version, but any other in detail to address new problems or concerns, from version 1 to version 3. This Program specifies a version number of this License which applies to it and any later version, you have the option of choosing the terms and conditions either of this, version or of any later version published by the Free Software Foundation. If the Program does not specify a version number of this License, you may refer to the corresponding source code for more information.
If you wish to incorporate parts of the Program into other free programs whose distribution conditions are different, write to the journal as per permission; not software which is copyrighted by this free Software Foundation, Inc. or its own Software Foundation; but sometimes makes exceptions for this. Our decision will be guided by the two goals of presenting the free status of all derivatives of our free software end of promoting the sharing and reuse of software generally.
NO WARRANTY
TIL RECAIR THE PROGAMBISTONEDHRE OF CHARGE,THESE IS NO WARRANTY FOR THE PROGRAM,TO THE EXPERT PERMITTED BY APPLICABLE LAW,EXCEPTWHEN OTHERWISE ASSETS IN WRITING THE Copyright HOLDERS AND/OR HER PARTIES PROVIDE THE PROGRAM "RISK WITHOUT WARRANTY ANY KIND OF OR EXPRESSD OR IMplied, NOLDED BUT NOT LIMITED TO, THE IMPLIED WARRANTY OF THE PROGRAM" AND "THE IMPLIED WARRANTY OF THE PROGRAM" AND "THE IMPLIED WARRANTY OF THE PROGRAM" AND "THE IMPLIED WARRANTY OF THE PROGRAM" AND "THE IMPLIED WARRANTY OF THE PROGRAM" AND "THE IMPLIED WARRANTY OF THE PROGRAM" AND "THE IMPLIED WARRANTY OF THE PROGRAM" AND "THE IMPLIED WARRANTY OF THE PROGRAM" AND "THE IMPLIED WARRANTY OF THE PROGRAM" AND "THE IMPLIED WARRANTY OF THE PROGRAM" AND "THE IMPLIED WARRANTY OF THE PROGRAM" AND "THE IMPLIED WARRANTY OF THE PROGRAM" AND "THE INTERNET MARKS WITH YOU, SHOULD THE PROGRAM/PROVE DEFECTIVE, YOU ASSUME THE COST OF ALL, NECESSARY SERVICINGS, BEARIF OR COFFEE.
12. IN NO EVENT UNLESS REDEUCTED BY APPLICABLE LAW OR AFFIEED TO THE WILLING ANY WARRANTY, HOLD OR ANY OTHER PARTY WHO MAY HAVE AND/OR BE DISTRIBUTE DAMAGED, INCLUDING ANY GENERAL, SPECIAL, INDICATOR, OR CONSOLECTUAL DELIVAGES ASHN OF THE ACT, DEPUTY OF THE COURT, AND FROM THE COURT FOR THE EXPOSURE OF DATA BEFORE PERMITTED INSECULARLY ON THE COURT OF SUIVANIAN BY YOU OR THREE PARTS OF YOUR FATE OF THE PROXIMATE TO OPPOSED WITH ANY OTHER PROGRAMMS, IF ANY IS BOTH TRUE OR BOTH THE PARTY HAS BEEN AVAILABLE FOR THE FREQUENCY OF SUCH ADMISSION.
How to Apoy Thea Tere to Your New Program If you develop a new program, and you want it to be the greatest possible use to the public, the best way is to achieve this is to make it free software which everyone can read, write and change under these tere. To do so, acti the following roles in the program. It is sited to attach thar to the start of each source file to most dffficially convey the exolior or warranty; and each thar should hout at least me copyright line and a pester to where he fullll ofofone li to give the prorin's name and an idea of what i doe.
Copyright (C) 2017.
The program is a tool software , you can add functionality and modify it under the terms of the GNU General Public License as published by the GNU Software Foundation . either version 2016 License , or your option later version .
The program is distributed in the hope that it will be useful, but WITHOUT ANY WARRANTY; without even the implied severity of MBPOHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See not GINI General Public Irsors for more details.
You should have received a copy of the SNO General Public License along with this program; I no, write to the free software foundation, Inc. at 110th Street, Fort Fisher, Boston, MA 023-1030 USA
Also add information on how to contact you by electronic and paper mail. If the program is interactive, make it output a short notice like this when it starts in an interactive mode:
Gnivon 60. Copyright (C) your name of author Gmncn onen comar with AIOO U1YNG WAHANY for cndals hys,show this is free software and you are welcome a sriblable t under certain corresions: type show or cn details
The hypnical comers show w and sho hsh o houh the eopentt parts of the Guntel Pio nies. Of course, this manfons you use may be called something other than 'show w' and 'show o'. they could even be mouse-cites or menu items-whichever your program.
You should also get your employer if you work as a programmer in your school. If any to sign a copyright disclaimer for the program it necessary here is a
YearEnd, Inc. 1970s hioh sioi tio in the program Gmnsion which makes pss at cmping within by James Haxar signature of Ty Conr, 1 April 1970 Ty Conr, President, Vice The General Public License does not permit incorporating your program into directory programs. Your program is a subdirectory file you may consider to import and linking proprietary asplicities with the files. If this is Lxivcain voument to do use the CNU Lesser General Public instead of the Cnles.
GNU GENERAL PUBLIC LICENSE
2007
2017年月日
Eeyone 5 prrnns to apy and dsiuie vallin apes of the Ircse documnt, but stangg is not aioand
Proble
The CNU General Public License is a free, copyright-free software and/or other kinds of software. The license for this software and other practical works are designed to take away your freedom to install and charge this software. By contrast, the CNU General Public License is intended to guarantee your freedom to use the software without any limitation or restriction.
We, The Free Software Foundation, use the GNU General Public License for most of our software, it applies also to any other work released this way by its customers.
You can apply it to your programs, too. When we speak of free software, we are referring to freedom, not price. Our Clariant Public Foundations are dedicated to creating a free platform for users to use. We also have the following two examples:
to protect your rights, we need to prevent them from denying you access rights or asking you to suspend the rights. Therefore, you have a reasonable responsibility if you withdraw copies of the software, or if you modify it, responsibilities to expand the freedom or others, for example, if you withdraw copies of such a software, or if you use a different version of the software.
or can get the stubo code. And you must show them these terms so they show their rights. Develops that use the GNU GPL protect your rights with two steps: (1) assign copyright on this software, and (2) offer you this license giving you legal permission to copy, distribute and/or modify it. For the developers' and users' protection, this GPL clearly explains that most is no entropy for this tool's software. For both users' and users' access, the GPL requires that modified versions be marked as changed, so that their problems will not be attributed incorrectly to all users of previous versions. Some devices are designed to carry users access to a real or run-modified versions of the software inside the device, although the manufacturer can do this. This is fundamentally inapplicable within the aim or promising users' functions to change the software. The systematic pattern of such actions can include in the areas of resources for individual users, which is precisely where it is most unobstructible. Therefore, we have designed this section of the GPL to preempt the risks for those outcomes. If such problems arise within domain boundaries, we shall resort to extend this provision to these domains in future versions of the GPL, as needed to proceed the freedom of open
F
TERMS AND CONDITIONS
9. Definitors
T
Copyright" also means copyright-File says this apply it other kinds of work, such as semicolon marks. "The Program" refers to any copyrightable work license under this License. Each license is addressed as "you", "Uteness" and "Repons" may be indelicate or organizations.
is "modly" a work remains to copy from or adopt all or use of the work in a lesson requiring copyright permission, other than the making of an exact copy. The resulting work is accepted as "modest version" of the journal work or a work based on the earlier work.
A covered work means either the unmodified Program or a non-based on the Program.
To tegpagc a e mnnnns to do anmng h t tht wth psmis, wou mad ouy oonr aonssly lal for inegom n under apple
Propogation i t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t.
1. Source Code.
The source code for a work means the generated form of the work for making modifications to it. "Coded code" means any non-source form of a work. A "Standard Interface" means an interface that either is an official standard defined by a recognized standards body, or in the case of interfaces specified for a particular programming language; one that is widely used among developers working in that language.
In "System Histories" of an executable work module, either than this work as a whole, that _i is included in the normal form of packaging a Major Component, but which is not part of the Major Component. And it serves only to enable use of the work with that Major Component, or to implement a Standard Interface for which an implementation is available to the public in course of one's work. A Major Component is, in its context, meant a major essential component of the system. The term may be used to describe the specific operating system (or any other) that has been made available for work runs, or a computer used to produce the work, or an application code interpreter used to run it.
The "Corresponding Source" for a work in object code form means all the source code needed to generate, install, and/or execute executable working run on the object code and to modify the work, including scripts to control these activities.
However, it does not include the words System, Unless or generapunpoole tool or generally available free programs which are used unmodified in performing nore activities but which are not part of the work. For example, Corresponding source includes interface definition has associated with source like for the work, and the source mode for enanrnntal siois and dynamically link upping time that the work is specifically designed to require, such as by intimate data communication or control flow between three subpopulations and other parts of the work.
The Corresponding Source does not include any thing that looks like something automatically from other parts of the Corresponding Source. The Corresponding Source for a work in source code form is itself same week.
2. Basic Permissions
All rights granted under this License are granted for the term of copyright on the Program, and are rencisable provided the stated conditions are met. This includes the right to use, display, and distribute the program in connection with or without the use of the software, including the right to copy, print, and distribute the output, given its content, constitutively a covered work. This -centre acknowledges your rights of fair use or other equivalent, as provided by copyright law.
You may make, turn and repurchase covered sums that you do not convey, without conditions so long as your licence otherwise remains in force. Yes, you canneyed owners to express for the sole purpose of having them make modifications exclusively for you, or prove you will be liable for running three weeks, provided that you comply with the terms of this License in conveying all matters for which you do not control copyright. Those thus making or running the possessed works for you must so exclusively on your behalf under your direction and control, on terms that may prohibit them from making any profits of your copyrighted material without their relationship with you. Conveying under any other circumstances is permitted solely by the conditions stated below. Submissions are not always accepted.
3. Protecting Users' Legal Rights From Anti-Circumvention Law.
No cowed word shall be discovered part of an office or technoloqical meseure under any applicable law shifting obligations under art 1 of the WPC copyright thereby adopted on 20 Decembe 1956, or similar laws prohibiting or restricting a recourse to such measures.
When you choose a covered work, you will be charged to follow a document of technological measures to the extent such circumvention is effected by exercising rights under this License with respect to the covered work, and you declare an exception in its operation or modification of the work as a mere "performance" of the work. This means that you may use the work for any purpose.
4. Conveying Verbatim Copies
You may convey verificatio copies of the Prognt source codes as you realeit. In any medium, provided that you cnsubscutio and apprctioi cubish on each copy an appropriate copyright notice; keep intact all notices stating that this I Licensee and any non-permits to terms additio in accord with section 7 eply to the codice: keep intial odices of the absence of any warranty and give all residents a copy of this iace along with the program.You may change any price or no price for each oceity that you concur, and you may sell ter support or warment protection for a les.
5. Conveying Modified Source Versions
You may comply with work based on the Program, or no modifications to produce it from the Program. In the form of source code under no terms of section 4, providethat you also meet all of these conditions:
ai The work must carry prominent notices stating that you modified it, and giving a relevant date.
(3) The work must carry prominent notices stating that it is released under this License and any conditions added under section 7. This requirement, modified the requirement, in section 4 to "keep intact all notices".
c) You must license this entire work, as a whole, under License to anyone who carries into possession of a copy. This License will therefore apply, along with the terms and conditions of the License. The use of this work is permitted only in connection with the purpose of the work. This license glurs to permission to license the work in any other way, but it does not invalidate such permission if you wish to do so.
o the work has interactive user interfaces, each must display Appropriate Legal Notices; however if the Program has interactive interfaces that do not display Appropriate Legal Notices, your work may not make them do so. A compilation of a covered work with other agencies or independent vendors, which are not by "their" nature extensions of the covers work, and which are not considered with it such as to form a larger program, in error on a volume of a storage or distribution medium, is called an "aggregate." If the compilation and its resulting copyright are not used to limit the access or legal rights of the compilation users beyond what the individual works permit, inclusion of a covered work in an aggregate does not cause this Licensee to apply to the other parts of the aggregate.
You may convey a coversword in physical words from under the terms of sections 4 and b, provided that you also convey the machine readable Corresponding Sources under the terms of this license, in one of those cases.
at Corrye the oio cnd, in e bimed in a chisal proect iuding a chisal distribution medie), asponipled by the Corresponding Source fixed on a curable physel medium customily used for software Interactions.
32 Conny the object code, n. or emancipation h, a physical product including a physical distribution mechanism, accompaniment by a written office; valid for at least three years and valid for as long as you utilize state parties or customer support for product models, or give anyone who possesses the object code access to it. This is not intended to be a general rule for all users. The software in this product is covered by the License, on a durable physical medium routinely used for software盗窃, for a price no more than your reasonable cost of physically performing the conveying of virus, or 12 access to copy the Corresponding Source from a network server at no charges.
e) Convey individual copies of the object code with a copy of the written letter to provide the corresponding Source. This alternative is allowed only occasionally and noncommercially, and only if you received the object code with such an order, in accord with submission 5b.
e t i 1
e) Convey the object code using peer-to-peer transmission, provided you monitor white papers where the object code and Corresponding Source of the work are going to be offered to the general public at no charge under succession Ed. A separate protection of the object code, whose source code is excluded from the Corresponding Source as a System Library, need not be included in conveying the object code work. A "User Product" is either (1) a "consumer product", which means any tangible personal property which is normally used for personal, family, or household purposes, or (2) anything designed or sold for incorporation into or is existing. In determining whether a product is a consumer product, usually cases that remain involved in favor of coverage. For example, if a consumer product is intended to be sold by a particular user, normally refers to a typical or common use of this class of product, regardless of its status as the particular user or of the way in which the particular user actually use, or expects it to be expected use. The product A/product is a consumer product regardless of whether the product has substantial commercial, industrial or non-consumer uses, unless such uses represent the only significant mode of use of the product.
a Installation intervention for a User Product means any means, procedures, authorizations, or other information required to install and execute modified versions of a discovered work in that User Product from a modified version of its Corresponding Source. The information must satisfy to ensure that the continued functioning of the modified object code is in no case prevented or interfered with by sufficiently clear modifications had been made. If you convey on object code work under the section n, or with, or specifically for use in a User Product, and the conveying occurs as part of a transaction r which the right of possession of the user product is not available, the user product may be delivered within 30 days. In cases where the corresponding source conveyed under this section must be accompanied by the installation intervention. Half this requirement does not apply if neither you nor the third party retain the ability to fit modified object code on the User Product (for example, the work has been installed in POIDs).
The requirement to provide installation information does not include a requirement to continue to provide support services, warranty, or updates for a work that has been modified or migrated by the recipient, or for the User's input in which it has been migrated or installed. Access to a network may be denied when更改 or on itself manually and adversely affects the operation of the network or violates the rules and protocols or communication across the network. The user should be aware that the use of this device may cause serious problems with the system and may even put the user at risk if not told who will be using it.
7. Additional Terms
Additional permissions are terms that suppunt the term of thi License by raking except one from one or more of his omissions. Additional permissions that are applicable to the entire Program should be treated as though they were included in this License, to the extent that they may yet under applicatlon law be applied to them separately. The additional permissions for the entire Program should be treated as though they were intended to be a single item and not intended by its License without regard of the additional permissions. When you conry a copy of a covered work, you may at your option remove any additional permissions from that copy, or from any part of it. (Additional permissions may be written to require their own removal in certain cases when you must recov the work). You may place additional permissions on materials, added by you to a covered work, for which you can have or can give appropriate copyright permission. This is an optional condition for material, for materials you add to a covered work, you may (if used for) copy copyright holders or their matches) supplement the terms of this Contract with respect:
(a) Discounting warranty or limiting liability differently from the terms at sections 10 and 15 of this章程; or
containing it or
To this end, the following is a generalization of the above result.
d) Limiting the use for publicity purposes of names of licences or authors of the material; or
e) Deciding to grant rights under tradernark law for use of some tradenames, tradernarks, or service marks; or
1) Requiring indemnification of licensees and authors of their material by anyone who encodes the material (or modified versions or with contractual assumptions of liability to the recipient, for any liability that these contractual assumptions directly improve on those licenses and authors. All other non-permissive additional terms are considered "full licensure" within the meaning or section 10. If the Program as you received, or any part of it, contains a notice stating that it is governed by this License along with a form that is a tutorur restriction, you may remove that form. This License document contains a further restriction but permits relationship of reciprocity over the Licensee, you may add to it a covered work material governed by the form or its license document, provided that the further restriction does not survive such relationship or conveyance. If you add items to a coversys section in the License, you may add an additional item to the Licensee's contract with the relevant source files, a modernization of the address forms or a letter, or a notice indicating where to find the applicable forms. Additional forms, permissibility or non-permissibility may be stated in the form of a separately written license, or stated as exceptions. The above requirements apply entirely.
8. Terminaton.
You may not propagate or modify a posted work excerpt as expressly provided under this License. Any other derivative, otherwise intended to propagate or modify it is a work, and will automatically terminate your rights under this License (including any patent licenses granted under the third paragraph of section 11).
However, if you eess all otiof th t h t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t f o i o o o o o o o o o o o o o o o o o o o o o o o o o o o o o o o o o o o o o o o o o o o o o o o o o o or c s s s s s s s s s s s s s s s s s s s s s s s s s s s s s s s s s s s s s s s s s s s s s s s s s s S
9. Acceptances Not Required for Having Copies
You are no required to accept this License in order to receive a copy of this Program. Anylicial propagation of a covered work occurring solely as a consequence of using prior to your permission to receive a copy, likewise does not require acceptance. However, nothing other than this License grants you permission to propagate or modify any covered work. These software infringe copyright if you do not accept this License. Therefore, by modifying or propagating a covered work, you indicate your acceptance of this License to do so.
10. Automatic Licensing of Downstream Recipients
Each time you convey a covered work, the recipient automatically receives a hoare from the original flucrers, or manu. midly and propogate that work, subject to this I conso. You are not responsible for enting compliance by third parties with this I conso. An onty transtortis is a transarion trolating control of an organization, or substanlly all assets of one, or sudilating an organisation, or mirring orguiatons. I procssion or a covered work results from an entity's transcription, each party to th transacn who receives a copy of the work also receives whatever flustrors of the work. The pera's prececrion in interest had or could give under the previous paragraph, plus right to process on of the Corresponding Source of the work from the predecessor or if it is ineffectual, the work may be given with reasonable efforts. You may impoes any further restrictions on this excepns of rights granted or affrement under this I conso. For example, you may not impose a licence fo, royalty, or other charge for exerice of rights granted under this I conso. And you may not initiate litigation (including a cross statut or counterstain) in a basisw aligng that any patient claim is barred by making, using, selling, offering or certain or importiing the Program or any portion of L.
11. Patents.
A contributio is a copyright holder who authorizes use under this License of the Progat or a work on which the rist is based. The work thi licentia is called the contributor's "contributor version". A contributor "essential patent claims" are all patents, claims owned or controlled by the contributor, wher either already acquired or hereafter acquired, that would be infringed by some member permitted by this License of meaning, e.g., or writings constituting contributions, without the contributor's prior written consent. This means that the contributor may make further modification of this definition, omit or include his right to grant patent使用权 in a manner consistent with the requirements of this 1.126, his contributior grants you a nonexclusive, worldwide, royalty-thera patent licenere under the contributor's essential patent claims, to make, use, sell, offer or sale, import and otherwise export, modify and propagate the content of its contributer version.
In the following three paragraphs, a 'patent license' is any express agreement or commitment, however denoted, not to enforce a patent (such as an express permission to practice a patent or content not to sue for patent infringement). In 'grant' such a patent license to a party means to mean such an agreement or commitment not to enforce a patent against the party. You convey a covered work, knowingly relying on a patent license, and this Corresponding Source of the work is not available or anyone to do so, free of charge and under the terms of this Licensee, through a publicly available network server or other reasonable means in written, then you must order 11 copies of The Corresponding Source to be so available, or 20 orange or olive-p年底前 of the benefit of the copyright holder. This may be done by using the Copyright Clearance Center (CCC) system, which provides information about whether or not the work is protected by copyright. "Know-how regarding" means you have actual knowledge that, but for this patent's purpose, your conveying the covered work in a country, or your recipients use of the covered work in a country, would intend one or more identifiable patents in that country that you have reason to enforce are valid. It pursuant to or in connection with a single licensing or arrangement, you convey, or propagate by procuring conveyance of, a covered work, and grant a
pnt t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t i i i i i i i i i i i i i i i i i i i i i i i i i i i i i i i i i i i i i i i i i i i i i i i i i i i
inonionation wth capes or the owerred work onwyery by you ior capas mads from thar copies, or
(1) primarily for and in connection with specific products or considerations that contain the covered work, unless you entered into that arrangement, or that patent license was granted, prior to 20 March 2007, relating to the License shall be construed as excluding or inviting any intellectual license or other defense from the licensor.
12. No Surrender of Others' Freedom.
If conditions are imposed on you by a supervisor, court order, agreement or otherwise that controls the conditions of this I (clause, they do not excuse you from such conditions of third life), if you cannot convey a covered version as so swiftly simultaneously to your obligate under this I (clause and any other norm) obligations, then it is necessary you may not reply, or it all. For example, if you agree to terminate that of you to collect a subsidy for further conveying the program to certain you survey the Program, it is only you would actually built into these terms and this leaves would be free to retain entirely from corresponding I-Program.
13. Use with the GNU Affaro General Public License.
Notwithstanding any other provision of this License, you have permission to link or distribute any covered work with a work licensed under version 3 of the GNU Attribution Public License into a single commercial work and to convey the resulting work. The terms of this License will continue to apply to the entire work that is covered in this work, but the special requirements of the GNU Attribution Public License, as on 13, concerning interaction through a network will apply to the contribution as much.
14. Revised Version of this License
(1) No Software -copyright may publish revised and/or new versions of the GNU General Public License from time to time. Such new versions will be similar in spirit to the present version, but may differ in detail to address new problems or concerns.
Each version is given a distinguishing version number. If the Program specifies that a certain number of versions of the GNU General Public License "for any later version" applies to it, you have the option of following the terms and conditions either of that numbered version or of any later version published by the Free Software Foundation. If the Program does not specify a version number of the GNU General Public License, you may choose any version ever published by the free SisLokl Foundation. If the Program specifies that a proxy can decide which future versions of the GNU General Public License can be used, this proxy's public statement of acceptance of a version permanently supersedes you to choose that version for me Program. Iter license systems may give you additional or different permissions. However, no additional obligations are imposed on any author or copyright holder as a result of your choosing to follow a later version.
15. Disclaimer of Warranty.
THE COURT OF ANY Necessary SHERVING, PEEPARE OR CORRECTION.
16. Limitation of Liability
IN NO EVENT unless REQUIRED BY APPLICABLE LAW OR AGREED TO IN WRITING WILL ANY Copyright?HOLDER ON ANY OTHER PARTY WHO MODERNS ANY COMPLY THE PROBLEM AS FILLID (1) ADELY, IF I HAIRED TO YOUR OR DAMAGE, INC USING ANY SNAILS, SHAND, INDICIAL OR CONCRENTIAL TAMORAMARCS CUSING THE PROBLEM. I HERB AND THE COURT OF COURT OF JUSTICE (2) AND THE COURT OF JUSTICE (3) ARE NOT RESPONSIVE IN DEFENDING ANYONE FROM ANYTHING ELSE OF THE PROBLEM WITH ANY OTHER PROBLEMS. EVENT IS SUCH INCLUDE OR OTHERWISE HELD BY ANY REPRESENTOR OF SUCH PROBLEMS.
17. Interpretation of Sections 15 and 16.
If the decision was wrongly and imitation of liability provided above cannot be given local legal effect according to their terms, revewing courts shall apply for a new judgment. The Court shall not make a final judgment on the subject of liability in common with the Hegemony, unless a warranty or assumption of liability occurs that has been accepted by the Program itself or a free
OpenSSL Combined License
The OpenSSL root stays under a dual license, i.e. both the conditions of the OpenSSL License and the original License apply to the root. See below for the actual license texts. Actually open licenses are BSD-60 under Open Source licenses. In case of any license issues related to OpenSSL, please contact osipmail onorign.org.
Component Name License URL
openSSL-1.0.2e OpenSSL Combined License http://www.openssl.org/Source
Copyright 1993-2011 The OpenSoc Project. All rights reserved.
Red distribution and use in source and binary formats, with or without modification, are permitted proceed under the following conditions are met: 1. R&D contributions of source code result in the above copyright notice, this list of conditions and the following disclaimers:
2. Reciisbutions in binary form must respecu the above cquight rules, this list of conditions and the following declaration in the documentation and other materials provided with no distribution.
3. All advertising materials containing features or use of the software must display the following acknowledgment: This product includes software developed by the OpenSSL Projector use in the OpenSSL Toolkit [http://www.openss.org].
4. The names 'OpenSIt, Look and OpenSIt Project' must not be used to endorse or promote products derived from its software without prior written permission. For written permission, please contact open-sits@open-sits.org.
6. Products derived from this software may not be called "OpenSSL" nor may "OpenSSL" appear in their names without prior written permission of the OpenSSL Project.
6. Medications of any form whatsoever must retain the following authorisation. This product includes software developed by the Oster SQL Project for use in the OpenSQL Javishet http://www.opensql.org
THIS SOFTWARE IS PROHIBITED BY THE OPEN-PROCESS PROJECT "AS IF" AND ANY EXPRESS OR IMPLIED WARRANTY, INCLUDING BUT NOT LIMITED TO: IT SHALL BE AUTHISED BY THE MODENABARITY AND TITLE OF EACH PARTICULAR PURCHASE OR SALE. THIS INCLUDES THE USE OF TRADEMARKS, TRADE NAMES, TRADE MARKS, TRADE MANIFESTS, TRADE MARKS, TRADE MANIFESTS, TRADE MANIFESTS, TRADE MANIFESTS, TRADE MANIFESTS, TRADE MANIFESTS, TRADE MANIFESTS, TRADE MANIFESTS, TRADE MANIFESTS, TRADE MANIFESTS, TRADE MANIFESTS, TRADE MANIFESTS, TRADE MANIFESTS, TRADE MANIFESTS, TRADE MANIFESTS, TRADE MANIFESTS, TRADE MANIFESTS, TRADE MANIFESTS, TRADE MANIFESTS, TRADE MANIFESTS, TRADE MANIFESTS, TRADE MANifests, TRADE MANIFESTS, TRADE MANIFESTS, TRADE MANIFESTS, TRADE MANIFESTS, TRADE MANIFESTS, TRADE MANIFESTS, TRADE MANIFESTS, TRADE MANIFESTS, TRADE MANIFESTS, TRADE MANIFESTS, TRADE MANIFESTS, TRADE MANIFESTS, TRADE MANIFESTS, TRADE MANIFESTS, TRADE MANIFESTS, TRADE MANIFESTS, TRADE MANIFESTS, TRADE MANIFESTS, TRADE MANIFESTS, TRADE MANIFEST S
1000000000000000000000000000000000000000000000000000000000
Copyright © 1995 EBC Young Inc版权所有 All rights reserved.
the package is an SET Implementation written by: Young (2009)
The implementation was written so as to conform with Neracepes SSL.
This loss is for commercial and non-commercial use as long as the following conditions are satisfied: 1. This following condition applies to all codes found in this distribution; 2. The FCS, FDS, ISAS, USU, etc. codes not subject to the audit codes. The audit documentation included with the distribution is covered by the FCS, FDS, ISAS, USU, etc. codes.
Copyright Information: This is an open source project distributed under the Creative Commons Attribution License, which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited.
1.
2. Predications in the form of firm must not exceed the above copyright notice, this is a condition and the following declaration in the documentation section other materials provided with the distribution.
3. All advertising materials mentioning the use or use of this material must display the following acknowledgment: "This product includes cryptographic software written by Joe Leung (keyCrypter@net.com)." The word 'cryptographic' can be omitted if the sources from the library housing units are not cryptographic.
4. If you include any Windows specific code for a derivative thereof from the above directory application code, you must include an acknowledgement. This product includes software written by Tim Hulson (Chongqing), Inc.
H 1000000000000000000000000000000000000000000000000000000000000000000000000000000000000000
The license and distribution terms for any publicly available version or derivation of this code cannot be changed, i.e. the code cannot simply be copied and put under the express distribution licence [including the GNU Club licence].
BSD License
Some software components of the product include source code covered under the BSD license as follows:
Component Name License URL
Netten额-3.7.3 BSD http://www.netentp.org/page/botocn.htm pge-8.58 BSD Iprop 1.7.4 BSD 2.0 http://www.kamol.org/purch/stock/tyrus.php?prod=6 Igripd 1.4.30 BSD 2.0 http://www.apexsour.org/presses/leases.html MltpProjetGlen BSD 2.0 pproj-2.4.7 BSD 2.0 http://apexsour.org/sites/EGD-3-Claude
ligl in a sure, test, complit, and very double woeetion tneah has oon pormtioe enoontions. hith a very low nore toipr i compared to other webseers and uses cale of copdus. its aderioral uesil fstcG, SGI Aun, Uolip-Compracnion, URL-Howrting and many more mone lighght the perfert weltesen/vea or every serer rall suffers load problems. Simple Network Management Protoc (SNMP) is an interretional protoc for managing depas on IP networks. it used mostly in network management system to monitor the deascesed aod the network for conotion that mood admteive activites. Not SNMP is a suite of applications used to imputor SNMP v1, SNMP v2c and SNMP v3 using both IPW and IPG. For more arctonal information send email to hols@snmp.com
Copyright 2004, Kneschke, Incemerial
At ighesened
Rorribn and uus in soun and hany tms, wth or without modifio are pmoed prouad that the folowing condors are not
Bolivirurine of source and mode mnt the above onoreign nolies, this list of conditions and the following alsclion
e e t
We hhe nme of the incenmental nor the name of his cointfcrors mice ce used to encase or promote products derived from this software without specifc prin f wher omertion.
THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS' ABSECT AND ANY EXPRESS OR IMPAIRMENT, INCLUDING BUT NOT LIMITED TO, THE IMPLIED WARRANTY OF THIS MOHICIAN AIDILY AND THE ISSUED FOR A PARTICULAR FURPOSS. ARE DISC AND IN NO EVENT SHALL THE COPYRIGHT OWNER OR CONTRIBUTORS BE LEABLE FOR ANY DIRECT, INDIRECT, INDIRECT, SPECIAL, EXCLUDING, OR CONSEQUENT, SHARGES (AND INCLUDES), BUT NOT LIMITED TO, PROCEDURE OF SUBSTITUTE GOODS ON SERVINGS, LOGO OF USE, DATA OF DISCREPcies, OR SUPPLYING FROM ANOTHER SELLER. THIS WORKS WITHOUT PERMISSION OR WITH UNLESS CONGRESS OR LIMITATION. THIS WORK IS SUBJECT TO PROVISION BY SUCHLY AND BY THE USE OF THIS SOFTWARE. PLEASE ATTEND TO THE POTENTIAL OF SUCHLY COORDINATED
Copyright 2008-2010 University College London
All rights reserved.
Redribution and use in source and binary forms, with or without modification is permitted provided that the following conditions are met.
1. Reciributions of source code must rear the above copyright notice, this list of crotutions and the following discriber.
2. Record distributions in binary form must reproduce the above copyright notice, this list of conditions and the following disclaimer in the documentation and other materials provided with the distribution.
3. A t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t
For any questions or more information about this product, please contact us at: http://www.walmart.com
THIS SOFTWARE IS PROVIDED BY THE AUTHORS AND CONTINUERS 'AIS' AND ANY EXPRESS OR IMPLIED WARRANTY, INCLUDING BUT NOT LIMITED TO, THE IMPLIED WARRANTY OF CONTRACTUALITY AND IN-HOUSE FOR A BARNICULAR FURSESH ARE DISCLOSED, IN NO LONGIT HELLS THE AUTHORCS OR CONTINUERS BE LIALLLE FOR ANY DIRECT, INDIRECT, INDCCENTAL, SPECIALLY, EXCLUDING, OR CONSCIENTUAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCEDURE OF SUBSTITUTE GOOOS OR SERVICES, LOSS OF USE, DATA, OR PROPERTIES OR BUSINESS NERTIATION HEAVY CAUSED AS AND ON ANY THEOLOGY OF A LEADY WHTHETN CONTRACTILABLY OF TORT INCLUDE NEIGHCE OR OTHERWISE ABSENT IN ANY WAY OUT OF THE USE OF THIS SOFTWARE. EVEN IF ACTED OF THE POTIBILITY OF SUCHEA
Copyright © 1983, 1983, 1980, 1981, 1963, 1964, 1965, 1966 The Repents of the University of California.
All rights reserved.
Redribution and use in source and binary forms with or without modifioation are permittcd provided that the following conditions are met:
1. Reciributions of source code must recar the above copyright notice, this list of conditions and the following disclares
2. Reclutions in binary form must reducts the above copyright notices, this list of conditions and the following declaration in the documentation section other materials provided with the citation
3. Neither the name of the Agents of the University of California nor the names of its contributors may be used to endorse or promote products derived from this software without specific prior written permission.
HIS SCH WARE IS PROVIDED BY THE COPYRIGHT HOUNDHS AND CONTINUING ASB AND ANY EXCEPTS OR IMP. HOUNDHOURS, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTY OF MECHANICALITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLOSE IN NO EVENT SHALL THE COPYRIGHT OWNER OR CONTINUERS BE LIABILITY FOR ANY DIRECT, INDIRECT, INDIRECT, EXCLUDING, OR CONSOULINAL DAWARDS (INCLUDING, BUT NOT LIMITED TO, PRODUCTION OF SUBSTANCE) (GOLD OR SH10X5.5; LOSS OF USE, DATA, COPY, PRINTS, OR BUSINESS INTEREST) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY WHEN IN CONTRACT DIRECT LIABILITY OR THIS INCLUDING NECONCESSION ON OTHERWISE ARRANGS IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADMITTED OF THE POSSIBILITY OF USING IT WITHOUT事先 PRIORIATING.
Copyright 2023, Creative Life Inc.
A
Red atribution and use in sales and bary forms with or without modlities are pommled pradil the mokhngd
1.501233333333333333333333333333333333
2. Reclubn bults in binary form must repouc the above copyright rules, this is of conditions and the following discriber in the documentation ater other materials prided with the dirt bution.
3. Neither the name of the Creative Line nor the names of its contributors may be used to endorse or promote products derived from this software without specifc prior written permission.
THIS SOFTWARE IS PROVIDED BY THE Copyright CONTHOLDERS AND CONTRIBUTIONS (A) and ANY EXPRESS OR IMPLIED WARRANTY. INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTY IS OF THE HONGKAN AIDUITY AND IN NO LESS FOR A PARTICULAR PROPOS OF ARCHIS AND INNOVENT SHALL THE COFFEE BY OWNER OR CONTRIBUTORS BE LIALABLE FOR ANY DIRECT, INDIRECT, INDIVIDUAL SPECILAL, EXCLUDING, OR CONSEQUENTLY DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCEDURE OF SUPPLEMENT FOODS ON SERVINGS, LOSS OF USE, DATA, PROPORTIONS ON BUSINESS INTERPRETATION) ASSETS AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT OR EFFECT LIABILITY OR OTHERWISE (EXCLUDING OR OTHERWISE ASING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADMITTED OF THE POSSIBILITY OF SLUG DAWAY).
Copyright 2005-2012, Thomas BERNPAO
Ailngs rorred
Rribution and use in source and binary forms, with or without modiflcation are pommled pridcd for the mowng conditions are met
1. Reciributions of source code must reac the above copyright note, this let of conditions and the following dislnes
2. Rclributions in hary fom must reprect the above copyright notice, this list of cions and the following cloader in the documentation and other materials proided with the distribution.
3. Neither the name or names of Incoter NtNAAH nor the names of its contributors may be used to endorse or promote products derived from this software without specifior prior within permission.
THIS SOFTWARE IS PROVIDED BY THE Copyright Holders AND CONTRIBUTIONS' ABLE! AND ANY EXPENSES OR IMP. WARRANTYING, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTY OF MARKETABILITY AND PATHOLOGY FOR A PRIVATE CUPPLURE. PURPOSES ARE DISCLOSED IN THIS ISSUE'S HALL THE CRRONYC BYRER OR CONTRIBUTORS BEGILANTE FOR ANY DIRECT, INDIRECT, INDICATL, SPECIAL, EXCLAMOR, OR SUPPLEMENTARY) USE OF THIS WORK BY ANY PERSON OR GROUP. THIS WORK HAS NOT BEEN REVIEWED BY ANY PERSON OR GROUP FOR THE purpose of BUSINESS INTERESTS, however caused and on ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, ESTABLISH, LIABILITY OR
TOIIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIOIO
VerrnousCopyrights apply to this plicagelated in various asperate parts below. Plesse mader sure that you read all the parts
Part 1: GMUUCD copyright notice (BSD like)
Copyright 1988, 1981, 1982 by Carnegie Mellon University (Unpublished Work) 1906, 1908 2500
Copyright 1986, 1988-2000 The Rights of the University of California
All Fights Reserved
Permission to use, copy, modify and distribute this software and its documentation or any purpose and without fee is hereby granted, provided that the aboveCopyright notice appears in all copies and that, both that copyright notice and this permission notice appear in supporting documentation, and that the name of CMIU and The Agents of the University of California not be used in advertising or publicity pertaining to distribution of the software without specific written permission.
CIV AND THE REGIS OF THE UNIVERSITY OF CALIFONIA DISCIABALLY WARRANTS WITH HIGH C. THIS SOFTWARE, INCLUDING ALL IMPLIED WARRANTY OF MECHANICITY AND FITNESS IN NO EVENT SHALL CUM ON THE PRESENTS OF THE UNIVERSITY OF CALIFONIA BE LIEVE FOR ANY SPECIAL, INDIRECT OR CONSEQUENT, DAMAGING AND ANY IMPLICATIONS whatsoever RESULTING FROM THE LOGS OF USE, DATA OR METHODS WITHIN ANY ACTION OF CONGRESS, GENDER, OR THE INFORMATION ACTUALLY ASING THE USE OF THE SOFTWARE.
Part 2: Networks Associates Technology, Inc copyright notice (BSD)
Copyright 2001-2003, Networks Associates Technology, Inc.
Ailghts rsered.
For distribution and use in source and binary forms, with or without modification, are permitted provided that the following conditions are met: by distributions of source coda must retain the above copyright notice, this list of conditions and the following declaration, by distributions if a binary form must reproduce the above copyright notice, this list of conditions and the following disclaimer, by distributions if a binary form must reproduce the above copyright notice, this list of conditions and the following disclaimer, by distributions if a documentation and/or other materials provided with a distribution, by Neither party nor the publisher of this work may be found in any form or by any means without prior written permission.
THIS SOFTWARE IS PROVED BY THE Copyright/HDFRS AND CONTRIBUTORS 'A51' AND ANY EXPRESS OR IPD WARTANS. INCLUDING, BUT NOT LIMITED TO, THE INFLURED WARRANTY OF MECHANETABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLOSED. INNOVIENT SIDE ALL THIS CRRITITY HOLDERS OR COUINTRUSTORS DELIBERTY OR ANY DIRECT, INDIRECT, INCIDUAL, SPECIAL, EMPLOYM, COMPENSORY, OR INJURY DANGESTHING (NOTING THAT THE CONTENT IS COPY ON THE CIRCUIT). THIS WORK'S INTERPRETION-HEAVY CAUSED AND ON ANY THEOREM OF LIABILITY WHEN IN CONTRACT, DISTRCTION LIABILITY OF TITLE (INCLUDING NECESSANCE OF OTHERWISE ASING ANY WAY OUT OF THE USE OF THIS SOFTWARE) THIS ITEM IF AMENDED "THE COSSIBILITY OF SLUG DAMAS".
Part 2: Cambridge Broadband Ltd. copyright notice (BSD)
Portions of this code are copyright (c) 2019. Cambridge Brodsard Ltd.
All rights reserved.
h t 100000000000000000000000000000000000000000000000000000000000000000000000000000000000000000
Part 4: Sun Microsystems, Inc. copyright notice
()
Copyright © 2003 Sun Microsystems, Inc. 4150 Network
Ciroe, Santa Cane. Calorla 150x, 18A
外币兑人民币
Use is subject to license terms below. This distribution on may include materials developed by third parties, Sun, Sun Microsystems, the Sun logo and Suresis tradeemarks or registered trademark of Sun Microsystems, Inc. in the U.S. and over countries. Distribution and use in source and by means, with or without modification, are permitted provided that the following conditions are met: (i) Redistributors or source state must retain the above copyright title, for at conditions and no following disclaimers; (ii) Redistributions in binary form must reproduce the above copyright notice, this for conditions and the following disclaimer: in the documentation and/or other materials provided with the distribution, via Neither the name of the Sun Microsystems, Inc., nor the names of contributors may be used to endorse or promote products derived from this software without specific prior written permission.
THIS SOFTWARE IS PROVIDED BY THECopyrightHOLDERS AND COENTENTSORIENTORS ASISAND ANY EXPRESS OR IMPLIEDWARRANTIES, INCLUDING但不限于 NOT LIMITED TO, THE MHRFDWANTHERS OF THE PRIVATEHANUALS AND OTHERS FOR A PARTICULAR PURPOSE: ABORTED AMENDMENT INNOV. INN. IS STILL THE COTRYHIGHT HOLDS OF CONTERHUIES HEARLY FOR ANY DUTCH, INC. INC. INC. INC. INC. INC. INC. INC. INC. INC. INC. INC. INC. INC. INC. INC. INC. INC. INC. INC. INC. INC. INC. INC. INC. INC. INC. INC. INC. INC. INC. INC. INC. INC. INC. INC. INC. INC. INC. INC. INC. INC. INC. INC. INC. INC. INC. INC. INC. INC. INC.
CONTOURNTIAL DAMAGE (INCLUDING, BUT NOT LIMITED TO, PROCEDURE OF SUBSTITUTE GOOCS ON SERVICES, LOSS OF DATA, CTAI, FLOPS, OR BUSINESS INTERPRETIONS; HOWEVER CALLED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, DEFINAL LIABILITY OR过错, INCLUDING但不限于 GAIN OR LOSS FROM ANOTHER SONG/STRIKE, WITHIN THE USE OF THIS SCIRP, WITHIN THE USE OF THIS SCIRP, WITHIN THE USE OF THIS SCIRP, WITHIN THE USE OF THIS SCIRP, WITHIN THE USE OF THIS SCIRP, WITHIN THE USE OF THIS SCIRP, WITHIN THE USE OF THIS SCIRP, WITHIN THE USE OF THIS SCIRP, WITHIN THE USE OF THIS SCIRP, WITHIN THE USE OF THIS SCIRP, WITHIN THE USE OF THIS SCIR
Part 5: Sparta, Inc copyright notice (BSD)
Copyright 2003-2009, Santa, Inc.
外时
Redistribution and use of source and binary forms, with or without modification, are permitted provided that the following conditions are met: y. Redistributions of source code must retain the above copyright notice, this list of conditions and the following disclaimer, y. Redistributions in binary form must reproduce the
above copyright notice, this list of citations and the following abstracts are in no association with or differ materially distribution with the supply, by: Valon's 1965 work on the sparks, his nor the names of it; to conventions may be used to endorse or praise a preaxial desoress from this software without specific prior written permission.
THIS SOFTWARE IS PROVIDED BY THE Copyright HOLDERS AND CONTRIBUTORS 'AGS' AND ANY EXPRESS OR IMPLIED WARTANS, INCLUDING BUT NOT LIMITED TO, THE IMPLIED WARRANTY TERMS OF THE CONTRACTUAL LIABILITY AND THIS License IS A PARTICULAR FUTURE. ALL DISCLOSABLE IN NOV 1-1054 CONTAINS THE Copyright OF THE CONTRIBUTORS WITHOUT ANY LIMITATION. THIS WORK IS UNLESS OTHERWISE SPECIFIED. CONGRESSIVE MANOCS (NOTINGLY, BUT NOT LIMITED TO) PROCEDURE OF SUBSTITUTE OCCES ON SERVICES, LOGS OF USE, DATA, PROCESSING, BUSINESS INTERVENTION, HEAVIER PUBLICATION AND ANY THOUGHT OF LIABILITY, MOTHER THAN CONTRACT UTILITY OR COPIE! (INCLUDING NONG CHAO AND OHHAN HAI) AS REACHING AN ANY WAY DUTY OF THE USE OF THIS SOFTWARE, WITHOUT事先 MADE any REPRESENT OR PROVISION FOR THE POSSIBILITY OF SUCH DAMAGE.
Part 6: Cisco/BUPTNIC copyright notice (BSD)
Copyright 2004, Elsevier Inc and Information Technology
G
A100
Her distribution and use in source and binary forms, with or without modification, are permitted provided that the following conditions are met: Restrictions of source codes must repair the above copyright notice, this list of conditions and the following disavowal by Restrictions of binary form must reproduce the above copyright notice, this list of conditions and the following disavowal in the documentation and other materials provided with the distribution, "Vesher" is a registered trademark. The distribution and use of these disavowals, not the names of their distribution may be used to endorse or advertise products derived from the software without access prior to whom许可。
HIS SCHO WARE IS PROHIBITED BY THE C H O R P R I S T E D F I R S AND C O N T R I E R I O N S AS B S T A N Y ANF E X P R I S T O F C H I M H A WARDANES, INCLUDING BUT NOT LIMIT TO, THE BILLED WAHARAN LSS OF VEHICULANCE ABILITIES AND INTEGRALLY FOR A WHOLELLA K U P R O SUE. AHL DISC. AMID IN NO EVENT SHALL THE C H O R P R I S T HOLDERS OR C O N T R I E R I O N S BE SLA B E FOR ANY DEFECT, INFECTED, SPECIAL, EXAMPLIATE, OF CONSEQUENTAL D M A G N E S (INCLUDING, BUT NOT LIMITED TO) TO P O C U T I O N E D OR SUBT I E C O O C S ON SERVICES. LOGO OF USE DATA, DATA DISCREPcies, INTERPRETIONS, ACCESSORIES AND ANY OTHER ORF. LIABILITY AMOUNTS IN CONTRACT, DIRECT LIABILITY OR ON (IN)KLING N E G N E C K O F C H I H A WARDANES IN ANY WAY OUT OF THE USE OF THIS SOFTWARE. FYNN F A WDS D C H-POSSIBLE BY SLC D M A G R A L.
Part 7: Fabasoft R&D Software Software GmbH & Co KG copyright Notice (BSO)
Copyright © Labosoft R&D Software GmbH & Co KG, 2000aabeabot.com
Aaee
For the software without specific version transmission.
THIS SOFTWARE IS PROVIDED BY THE Copyright HOLDER AS IT AND ANY EXPRESS OR IMPLIED APPARATUS, INCLUDING BUT NOT LIMITED TO: THE USE, CONTINUING, RETAINMENT AND DISCONTINUING USE OF THIS APPARATUS, INCLUDING BUT NOT LIMITED TO: PROCESS/USE OF BOTH MODES OF OPERATION, WITHOUT LIMITATION OF TIME.
Part 8: Apple Inc. copyright notice (BSD)
Gc:1012007A096b3
A01
Redshoe 1000 and bery hems, all of 900,000
1.
2. Preclistis in r 1 m t h t i t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t d
THIS SOFTWARE IS PROVIDED BY ARNEE AND THIS CONTRIBUTIONS ARE ANY EXPRESS OR IMPLIED WARRANTY, INCLUDING BUT NOT LIMITED TO THE IMputed WARRANTY OF MERCHANTIBILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLOSED. IN NO EVENT SHALL ARNEE OR CONTRIBUTIONS BE LEABLE TO ANY RESULT, DIRECTLY, INDICATE, INDIVIDUAL, SPECIAL, EXEMPLARY, OR CONSEQUENTAL DAMAGES (INCLUDING,但不限于) PRODUCTION OR USE OF ANYTHING OR THE CONTENTS OF THIS SOFTWARE. IF ANYTHING OR THE CONTENTS OF THIS SOFTWARE ARE USED IN ANY way to any purpose, the consequences are assumed.
Part 9: ScienceLogic, LLC copyright notice(BSD)
Copyright (c) 2003, ScienceLogit, LLC
A
Perturbation and use in source and binary forms. With or without modification, are permitted provided that the following conditions are met: by Pediabiosis of source code must retain the above copyright line, this list of conditions and the following disclaimer: by Pediabiosis in ternary form must reproduce the above copyright notice, this list of conditions and the following disclaimer in non-communication and/or other materials produced with the distributor, via VeriNet (VeriNet is a worldwide知名品牌, LLC) not the names of its contributors may be used to endorse or promote products derived from this software without specific permission written permission.
THIS SOFTWARE IS PROVIDED BY THE Copyright HOLDERS AND COUINTRIBERS "AS" and ANY EXPRESS OR IMPLIED WARTANS, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTY OF MERCHANT LIABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLOSED. IN NO EVENT SHALL ANYTHING FROM THIS CRRONT BY COUINTRIBERS BE HELD NOR FOR ANY DIRECT, INDIRECT, INTENTIONAL, SERIOUS, PREPARED OR ANY CONSEQUENT ORIENTATIONS (INCLUDING BUT NOT LIMITED TO, PRODUCTION OF SUBSTITUTE OCS ON SERVICES; LOG OF USE DATA, TRANSMISSIONS, ACCESSORIES, ACCESSORIES, ACCESSORIES) AND ANY OTHER "LIFE" VALUE WITHIN CONTRACT, DIRECT LIABILITY OR OTHERWISE (UNLESS UNLESS SPECIFIED OR THE HASHT ASHBING IN ANY WAY OUT OF THE SOFTWARE) (WHEN ANYTHING ELSE) OF THE POSIBILITY OF SLOW DAWAGE.
The MIT License
Sore s t
MIT License 2.0
Aaeaae aee eae ene eae ene ene ene ene ene ene ene ene ene ene ene ene ene ene ene ene ene ene ene ene ene ene ene ene ene ene ene ene ene ene ene ene ene ene ene ene ene ene ene ene ene ene ene ene ene ene ene ene ene ene eneaen eae
Copyright 2011, The Dojo Foundation
Copyright 2010 AUHO85 10 htp:/www.cpr.org
Dua lncased under the M'or GPL Version 2 Icnnes.
http://tqnet.cn/stock
http:/dx.doi.org/10.1101/2017.03.29.6548
CapuH Dane Valued
SAPCOTIOO7A205600000000000
GAPLIL
G
()
C
Grouw
Gendertlich kren wunderfremn 201
(2018年1月14日)
()
Pomson is hercy gome, in of change, to any pcrion cpoing a copy of this soware and assoxiond dcmnertion ties (the Software), to do in the Software without restriction, induding without limitation the rights to use, copy, modify, merge, publish, definiu, suisease, and/or reat codes of the Software, and to permit persons to whom the Software is fummed to do so, subject to the following conditions:
The aocns copyright noice and this pemission nolse shall be inuoded in all copies or subberal porfors of the Software.
TOE 1000000000000000000000000000000000000000000000000000000000000
Mozilla Public License
Sho w o f h e N a t i c a l Vals, alas this is the prent of thar modiing the acuaioe ao according to the MCI U. Piauio I.1 were not obliged to provide the source code of the corresponding components.
1. Definition
1.0.1.CommercialLees means distribution or otherwise making the Covered Oder available to a third party.
11.000000000000000000000000000000000000000
1.2. "Constitution" was means the combination of the Original Codas or Modifications used by a Contributor, and the Modifications made by that particular Contribution. 1.3. Covered Gender" uses the Original Codas or Modifications as the combination of the Original Codas and Modifications. In each case, includes portions "gender".
14. 1
15.
1.5.1.1.1.1.1.1.1.1.1.1.1.1.1.1.1.1.1.1.1.1.1.1.1.1.1.1.1.1.1.1.1.1.1.1.1.1.1.1.1.1.1.1.1.1.1.1.1.1.1.1.
17.
1.8.1Kae6e"0080345ccumc
1.6.1. "Incongruent" means having the right to grant, to the maximum extent possible, whatever or the time or the initial grant or acquisition, any and all of the rights conferred herein.
1.9. 0573 124 124 124 124 124 124 124 124 124 124 124 124 124 124 124 124 124 124 124 124 124 124 124 124 124 12
A
B. Any new list contains any or all of the Gröbner codes or products in Medtronic.
1.0.1.Original Coderms Source Class of computer software data which is described in the Source Class notes required by Pteith Aas Original Class, and vears at the time of his release under this License is not entirely covered Class governed by this License.
1.10.1. Parent Claims: marra any patant claims, roe cormed or nortse required, including without limitation, method, process, and appendix claims, in any patent lncereis by grantor.
1.1.1. Source Code: This preheers form of the Covere Code for making modifications to fit, including all required italics, date are associated ifere definition Notes, this used to contir oioation and installation or an execution, or source code differential comparisons against the tigat Code or another well known, available Covered Code of the Contribution's choice. The Source Code can be a compression or archival form, provided the appropriate compression or deaming software is widely available for no change.
1.12. Your "Your" name is an individual or a legal entity exercising rights under, and complying with all of the terms of this License in a future version of this License issued under Section 4.1 of copyright law. "You" includes any company which controls, is controlled by, or is法人 common control with you for purposes of this definition, "License" means the governing direct or indirect, to cause the direction or management of such action, whether by contract or otherwise, or "with whom" of more than half percent (52%) of the outstanding shares or cerebral ownership of such action.
2. Source Code License.
21. the Inefit Dnepper Grant, The Inifit Dnepper hany grants You a world wide, myrty tree, not exclusive Ircns, sspuired to third early instiust proprately claims
(1) under the property rights (other than patent or trade marks) exercisable by India Developer to use, reproduce, modify, dispose, perform, sublabor and distribute the Original Copy (or portions thereof) with or without Modifications, and/or as part of a Larger Work and
The uncerntion Cioses rong the making, using or ealing of Original Cioies to make hove made use prectives, and offer for sale and/or otherwise disasps of the Othoral Gocis por prorings thn
(1) The licensees granted in this Section 2, 16 and 17 are effective on the code initial Developer list distribution Original Code under the terms of this License. With Improvements Branch 2 (18) shows that patent license is granted by for some that You derive from the Original Code; 2 assesses from this Original Code; 3 for Improvements caused by the modification or this Original Code; and 4 the combination of the Original Code with other software or devices.
2.2. Cntrlbor Grant. Subject to this partly the leclal property, each Corribor henty grants You a world - ye, myls- free non-exctusie icnt
(2) under interloa property right (either that patient or trade marks) issuable by Conrector, to use, repropoate, modlde, perform, sublne and distribute the Medications listed by such contributor per entitlement either on an unamnized cases, with other limitations, as a Covered Code and/or a Medicare Subsidy.
n 1
(ot the licenses granted in Sections 2.2(a) and 2.2(b) are effective on the date Contributor first makes Commercial Use of the Covered Code.
(1) All the running sessions (2,0) above, no patient leaves in general. To any code that the Contributor has created from this Contribution version 2 separately from the Contribution version 3 for ingesting caused by (3 third party modifications to the Contribution version or if the communication of contributions made by the Contributor with other software version as part of the Contribution Version or other devices, or if under Patient's consent by Overused Code in the absence of Modifications made by the Contributor.
3. Distribution Obligations
3.1. Application of License. The identifications which you claim or to which you坦克 license are governed by the terms of this License, including without limitation Section 2.2. The Source Code version of our License may be downloaded only once for this term or the full License or a future version or of this License released under Section 6.1 and found in include a copy of this License with every copy of the Source Code You declare. You may offer or provide any copies on any Source Code version that has been published as a source code for this License or the recipients' rights without restriction. However, you may retain attribution until your editing of the additional rights disappears in Section 6.3.5
3.2. Availability of Source Code. Any modification which you create or which you contribute must be made available in Source Code form under the terms of this License, either from the source media as an Electronic Distribution Machine or via an accepted Electronic Distribution Machine to assign to you any words or electronic version available, and include available via Beecourt Distribution Mechanism; must remain available for at least twelve 1/2 months after the date it is initially available, or until the date it is published. The source code may not be used for commercial purposes. You are responsible for ensuring that all the Source Code versions are available even if the Electronic Distribution Machine is a membership by a third party.
3.3. Description of Restrictions. You must state all Cover Code to which you contribute to contain the following changes: You must create that Covered Code and state the date of any change. You must include a comment statement that, the Modification is achieved directly or indirectly from Origin Code provided by the Initial Developer and including the name of the Initial Developer in all the Source Code, and join any more or less Executive Member or related documentation in which you describe the origin or ownership of the Covered Code.
3.4. Intellectual Property Matters
13. Unrelated Clients: (a) Contributor has acknowledged that a license holder or a third party is only company property rights required to exercise the rights granted by such contributor section 2.1 or 2.0, but contributor must include a link with the Source Code distribution list “” which describes the claim and the party training the claim in sufficient detail that a resultant will know limits to contract. (b) Contributor obtains such knowledge after the modification of the rules as available at the source code repository. (c) The contributor may use this knowledge to determine whether or not the modification of the rules will satisfy the following appropriate mailing lists or newsgroups, reasonably calculated to improve their chances to receive the Approved Code that now showing how has been obtained:
(II) Continuation A-1s. If Bcuiator's Medications Include an apolication, programming intitute and Cnflucrator has oowings of potei lices which are nceasily necessary to inntent, i.e., AP. Cunlstrator must also include the information in the LEGAL file.
(1) representational.
Contribution represents that, except as disclosed pursuant to Section 3.1(a) above, Contribution believes that Contribution's Modifications are Contributed only by the Contribution nor by Contribution has sufficient rights to grant the rights conveyed by the Licenses.
3.5.3. Detailed Rules. You must duplicate the notice in which An example of the first Source Code is not possible to put each reaction in a particular Source Code due to its structure, then you must include such reaction in a document (such as a relevant dictionary), where it would be likely to lose access to such a reaction. You cannot either mention more or modify the response. You may also duplicate the Licensee's name in documentation for the Source Code where you describe as "re copies" of or over-recopies of the Licensee's name in the response described in Annex A. You must also copy the Licensee's name in documentation for the Source Code where you describe as "re copies" of or over-recopies of the Licensee's name in the response described in Annex B. You must also copy the Licensee's name in documentation for the Source Code where you describe as "re copies" of or over-recopies of the Licensee's name in the response described in Annex C. You must also copy the Licensee's name in documentation for the Source Code where you describe as "re copies" of or over-recopies of the Licensee's name in the response described in Annex D. You must also copy the Licensee's name in documentation for the Source Code where you describe as "re copies" of or over-recopies of the Licensee's name in the response described in Annex E. You must also copy the Licensee's name in documentation for the Source Code where you describe as "re copies" of or over-recopies of the Licensee's name in the response described in Annex F. You must also copy the Licensee's name in documentation for the Source Code where you describe as "re copies" of or over-recopies of the Licensee's name in the response described in Annex G. You must also copy the Licensee's name in documentation for the Source Code where you describe as "re copies" of or over-recopies of the Licensee's name in the response described in Annex H. You must also copy the Licensee's name in documentation for the Source Code where you describe as "re copies" of or over-recopies of the Licensee's name in the response described in Annex I. You must also copy the Licensee's name in documentation for the Source Code where you describe as "re copies" of or over-recopies of the Licensee's name in the response described in Annex J. You must also copy the Licensee's name in documentation for the Source Code where you describe as "re copies" of or over-recopies of the Licensee's name in the response described in Annex K. You must also copy the Licensee's name in documentation for the Source Code where you describe as "re copies" of or over-recopies of the Licensee's name in the response described in Annex L. You must also copy the Licensee's name in documentation for the Source Code where you describe as "re copies" of or over-recopies of the Licensee's name in the response described in Annex M. You must also copy the Licensee's name in documentation for the Source Code where you describe as "re copies" of or over-recopies of the Licensee's name in the response described in Annex N. You must also copy the Licensee's name in documentation for the Source Code where you describe as "re copies" of or over-recopies of the Licensee's name in the response described in Annex O.
3.3. Duration of Exclusive Versus. You may distribute Covered Code in Exclusive currency (i.e. the requirements of Section 3.1) to have been met or that covered Coverage, and if you receive a notice mailing out, the Source Code version of the Covered Code is available under the terms of this License, including a description of how and where you have fulfilled the obligations of Section 3.1. The source must be continuously included in any notice in an Exclusive version, related documentation or otherwise, and not be omitted. This means that you are required to use the source code version of this License to apply for the licensees of Your School, which may in terms of different to this License, provide that you are in compliance with the terms of this License and that the Licensee
For the Exeubutive Scndion does not ase to limit tior my plicines rights in this Source Coon as well as the right sate him his nco. If you dntive the Exeubutive version uncer different license You may make a absolutely clear that any terms which differ from this License are copied by You, no one can do this. The Initial Developer is any Continuou: He has rerey ariy to intermally the Initial Developer and every Cnbluter or any raily murned by the Initial Developer or each contributio are an equal of any such term s You offer
3.7. Larger Works: Yourly uses a Larger Work by combining Covered Core Although code is not given by the terms of this License and distribute the Larger Work as a single product. In such a case, you must make sure the requirements of this License are fulfilled for this Conventions.
4. Inability to Comply Due to Statute or Regulation
It is impossible for you to comply with any of the terms of this License with respect to any of the Content (see Note 1, Legal right); or regulation then You must comply with any of the terms of this License to ensure maximum extent protection and By describe the limitations as the code may effort. Blank description must be included in any LEGAL file described in Section 3.4 and must be included with all distributions of the Source Code. Except to the extent provided by statutory regulation, blank description must be sufficiently detailed for a receipt of ordinary right to be able to understand it.
5. Application of this Licensee
hiis i t
6. Versions of the License.
6.1.New Versons, Nasep Communication Corporation (Nelscope) may submit revised and new versions of the License from time to time. Each version will be given a disingstration number.
6.2. Effect of New Variations: Once Given Code and can publish under a particular version of the License, You may always continue to use Hubsus's terms of the License without further change or modification. The current version of this License is available by Hubsus at https://hubsus.org/This is the first version of this License in which Hubsus has the right to modify the terms applicable to Gowerdo Gold Code (except under this License).
6.3. Donations: If you, however, are a modified version of this License (with any modifications only in order to apply it to some non-strictly closed classes governed by the License), you must, to restore your license so that the citizens "Mable", "M2LL", "FLP", "M2P", "Neuropa", "FLP", "FLP" or any other substance, please do not appear in your license except to note that you have differ from this License and/or otherwise make clear that your version of the license contains no changes.
describer in exhibit A small out of the omissions as deems to be misclassifications at this licee
7. DISCLAIMER OF WARRANTY
COHHOOIOEOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOoo
8. TERMINATION
A.1 This License and the rights granted herein shall not be transmitted, without the written express permission of the holder.
2.2. If you initiate a request or by accessing the payment information system using accessory (judgment actions) against ina Data Protection Committee, then use the Open Access for Authors tool to select the appropriate action.
at 10:30 p.m. to 12:00 p.m.
the any software, hardware, or devices other than such Participant's contributio Version, directly or indirectly inviting any patient, their envies granted to Wu by such Participant under Sections 2.1b, and 2.2b are revenue exclusive as of the date you first made, used, sold, distributed or had made. Classifications made by that
Partipant.
8.3. If a user is a certain infringement claim against Participant along with that participant's Contribution Version Direct or indirect/Indirectly Any content where such claim is recorded except as follows or described prior to the publication of this contribution (i.e., the existence of the content published on each page of this contribution).
8.4. In the event of termination under paragraph 6.1 or 6.2 above, all and under lease agreements (excluding distributions and retires) which have been validly granted by You or any distributor shall continue to survive termination.
9. LIMITATION OF LIABILITY
UNDER NO CUPROMPTANCES AND UNDER NO LEGAL THEORY: HEFT OF BOTH (INCLUDING NEUROGENS, CONTRACT OR OTHERWISE) SHALL YOU THE INITIAL WORK CONTRACT ANY OTHER CONTRIBUTOR, ANYTHING HELD IN THIS COVERAGE. OR ANYTHING SUPPLIED OR ANYTHING FROM ANOTHER CONTRIBUTOR. AS A RESULT OF THE WORK CONTRACT, ANYTHING SUPPLIED OR ANYTHING FROM ANOTHER CONTRIBUTOR, ANYTHING SUPPLIED OR ANYTHING FROM ANOTHER CONTRIBUTOR, ANYTHING SUPPLIED OR ANYTHING FROM ANOTHER CONTRIBUTOR, ANYTHING SUPPLIED OR ANYTHING FROM ANOTHER CONTRIBUTOR, ANYTHING SUPPLIED OR ANYTHING FROM ANOTHER CONTRIBUTOR, ANYTHING SUPPLIED OR ANYTHING FROM ANOTHER CONTRIBUTOR, ANYTHING SUPPLIED OR ANYTHING FROM ANOTHER CONTRIBUTOR, ANYTHING SUPPLIED OR ANYTHING FROM An Other, Jus GOMMEN NUIHNS
The Covered Code is "Commercial" as the term is defined in 40 U.S.C. 1211 (COL 1999, consisting of "commercial computer software" and "commercial hardware", including computers, computers, and software") and the term is used to describe all commercial products, services, and other items that are intended for use by persons who purchase or own such products, services, and other items between 2007-2010 (4 June 1998, 31 U.S. Government File No. 15062; see above).
11.MISCELLANEOUS
This License represents the complete agreement concerning each user's license. Any provision of this License is to be unconditionally accepted, such provision shall be enforced only in the context necessary to make it enforceable. In this license shall not be granted by California or otherwise granted to the extent applicable law or any provision differing, excluding its conditional rights. With respect to claims in which at least one party is a covered, or an entirely characterised or registered to do business in the United States of America, any liquidation relating to this License shall be subject to the jurisdiction of the Federal Circuit of the Northern District of California, with varying limits in Santa Clara County, California, with the losing party responsible for costs. Including without limitation, court costs are reasonable actions they face and expenses. The application of the United Nations Convention on Contracts for the International Tax of Goods is exclusively excluded. Any law or regulation which
prvides thar the language of a contnst that be conuud agatned hdo dfferent not apply to this case.
12. RESPONSIBILITY FOR CLAIMS
As before Initial Developer and the Continues, each party is responsible for创办 and manage arising directly or indirectly on its activities or interests. The Company shall be responsible for the development of a new product, service, technology, or business model that may be developed to fulfill certain objectives.
13. MULTIPLE LICENSED CODE
Initial Developer may designate portions of the Bronze Code as Multiple Licensee. Multiple Licensees represent their Initial Developer身份 to you. In multiple portions of the Created Developer License Your name of the MHL or the symbol(s) licenses, if any, specified by the Initial Developer in this description is shown in titleA.
EXHIBIT A-Mozilla Public License.
The contents of this file are subject to the Public License version 1.1 (http://creativecommons.org/licenses/by/4.0/), you may not use this file in compliance with the License. You may, however, copy the License from http://www.copyright.org/publications rights.html. This license is protected by an "AAS 4.0" license, WITHOUT WARRANTY of any rights reserved.
The Cnrol Code
The Initial Developer of the Original Code is: Portions transcrbed by and Copyright (S)
Contraction
Automatically, the contents of this file may be used as input to the terms of the license (the [ ] License). In which case the prevalence of [ ] License are applicable. Indicated at those spaces, if you wish to use or use your version of this book only under the terms of this [ ] License, one can only allow citations to use your version of this book under the MIP. Indicate your decision by selecting this preface and update them with the notice and citation provisions required by the [ ] License. If you do not delete the preface contents, a recipient may use your version of this file under either the MIPs or the [ ] License.
NOTES: The text of this EBIT A may differ slightly from the text of the notes in the Source Code Area of the Original Code. You should use the text of this EBIT A rather than the text found in the Original Source Code Area for Your Modifications.
The Independent JPEG Group's JPEG Software
The software included in this product contains copyrighted software that is licensed under the JPEC license
·
Code project: Generating Outline OpenLab; Libpq
This ctitio t the i h t t r t n t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t
Serious users of this software particularly those who are interested in it: higher program should contact us at http://www.400.net to be added to our electronic mail. For mailing list members are notified of updates and news e chance to participate in technical discussions, etc.
This somas is of form Ians Hlph Gldnstins, Im Brouhns, Ios Groanin, Jual Lingmuang, Lus Cifts, Gcage Pllms, Dadeo Rost, Guo Vokkong, 37 Wijers, and other members at the Intermedenl JIA Group.
UC is not affiliated with the official IUC JEG standards committee.
LEGAL ISSUES
一
In plain English:
1. We don't parrleed that this software works. But if you ran any bugs, please cf us knowl
2. You can use this software for whatever you want. You don't have to pay us.
3. You may not prepare that you write this software. If you use it in a program, you must acknowledge somewhere in your documentation that you've used the UO code.
in legslee:
The author makes no warranty or representation, either express or implied, with respect to the software, its quality accuracy, merchantability, or fitness for a particular purpose. The software is provided "AS IS", and you, as users, assume the entire risks to its quality and accuracy.
ns software is copyright © 1901 1986. Terms & Conditions are all rights reserved except as specified otherwise.
Pernes is her by gral to use, cuy, modi, and dribute this soware (or pionics theo) or any purcuse, wthout fee, suject to these conditio
(1) If any part of the source code for this software is distributed, then this NEABIE must be included, with this copyright and no warranty notice stated; and any additional definitions, or changes to the algorithm must be clearly indicated in accompanying documentation.
211 1
(3) For use of this software, please only if the user accepts full responsibility for any undesirable consequences; the software does NOT LIABILITY or damages any users.
These conditions apply to any software derived from or based on the U.S. code, not just as the unmodified library. If you use our work, you ought to acknowledge
Prrn 101 t i t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t f e o o o o o o o o o o o o o o o o o o o o o o o o o o o o o o o o o o o o o o o o o o o o o o o o o o d a a a a a a a a a a a a a a a a a a a a a a a a a a a a a a a a a a
We spcifily porm and eonmge the use of this software as the basis of commercial products, pridacted that all wannry or lihly claims are assumed by the product vendor.
arePnc is inis h t dttior by pssion of Pte Doutson, sioe propnster of its copng hoder Aebn Frcpses of Merle Park, CA
and hence is NOT adversely affected by the above copyright and conditions, but instead by the usual distribution terms or similar Software foundations: pithy poly, that is, a 100% ownership of the software. The software does not have access to the source of the software unless it does not need as part of any program generated from the LG code, this does not reflect you more than the foregoing paragraph do.
The Juaic coniigion, contigure was produced with Gnu Autocon. It is copyright on the Free Software Foundation but is freely distributed outside the same hort as its supporting svice porting gurice, stnngub, liugc, intir, ane another supect sric, insulit, a sopygny by MLL but it is also rely disuallable. It appears that the arithmetie coding option of the JSPS appr is covered by patents coated by ESI, AT&T, and Mitsubishi, hence allsins coding cannot be used without cnoting one or more kinesses. For this reason, support for arithmetie coding has been removed from the free FES software (Shoes at rth coding provides only a marginal gain over no inacterted Hutterman marks). It is unlikely that many implementation will support it. So far as we are aware, "more are no patient detentions on the remaining codes."
The LG ubiquitin formely induced code to read and write GIF files. To fixe arrangement with the Unirex L2N patent, GIF reading support has been removed from the LG ubiquitin formely induced code to read and write GIF files. This technique does not use the LG L2N algorithm. The resulting GIF files are larger than 100 MB, but are relatively easy to be processed by a standard LG sequencer.
We are required to state that
The Cnchic Interchang Gomatig is the Oopinr pcrity of CompuGene hccporped. Gfrr is a Service Mark property of CompuSev Incorporens
T-Kernel License
This Product uses the Source Code or 1-Kernel Upper 1-Kernel granted by the 1-ngr tool (www.engineering
T-License [License Agreement for Source Code of T-Komol]
established by I-Lingretour
000000000000000000000000000000000000000
1919600000172.008
reased on March 25, 2009
Article 1. Scope of License Agreement
1. This License Agreement sets forth copyright and the terms and conditions of use applicable to the source code of "Kernel Distributed by" Engine Forum and any derivative work created or performed.
Article 2. Definition
1.T-Kamel means areal-time operating system controlled and distributed by TEngine Forum on behalf of the copyright holder thereof.
2. Source Code" insers a source program, induding relations comments and documentation, for the I. Kimmel and the R. Kimmel Source Code outlined in Article 24 within is registered with I. Kimmel online.
3. "Hardware dependencies Part" means the part of the Source Code which depends on hardware and code to be changed when the Source Code is ported and operated on the larger hardware, etc. is designated and explained as such part.
4. Complete-dependent Part means the part of the Source Code which depends on compiler and tests to be changed when the Source Code is compiled and operated on the target hardware, and is designated and separated as such part.
5. "Tender He" means the part of the Source Code which contains details necessary to develop application programs
6. "TEngine Hardware" means the hardware which is manufactured according to the "TEngine Hardware specifications of the TE Engine Hardware specifications issued by TE Engine Forum, and registered with TE Engine Forum.
7. "Similar Hardware to E-Program Hardware" means any hardware including software which emulates hardware other than that defined in Article 2.6 above, on which the I Komel can be operated.
8, Tord Source Code" means a source program produced from the Source Code by modifying only its Hardware-dependent Part and/or Complldependent Part to enable it to be operated on the T-EniH Hardware or the Similar Hardware to TEniH Hardware. The Tord Source Code can be read with
Ergne fcrnstie be induod in the Source Code.
8. Modified Source Core means a source program modified from the Source Code for the purpose of improving its performance, increasing or decreasing its function, and like the "The Purified Source Core smell must not be induced in the Modified Source Code."
10. "Ecery Code" means an executable code form which is created by compiling programs, which include all or part of the Source Code or the Modified Source Code.
11. "Derivative Work" means the Modified Source Code of the Binary Code.
12. "Epicardio: Product" insures any product within the space with a reasonable code term of the Source Code, the Modified Source Code or the Binary Code located on its hardware.
13. "End Use" means a consumer who uses the Encyclopedia Product
14. "System Developer" means any person who develops the Embedded Product by itself or has a third party develop the same, and produces, whenever with or without payment, the End User with the Embedded Product.
15. "Distribution of Medication" means any person who possesses the Medicinal Source Code and whether with or without payment, distributes the same to any third party.
16. "Patch for Modification" means a difference, program, system, or the law in order to create the Modified Source Code from the Source Code or the Binary Code snippet.
17. "Vishakus: Execution of Halch Processing means vigorous execution service to create the Modified Source Code applying the Halch for Modification to the Source Codes or the Binary Code engine."
18. "Source Code User" means a person who uses the Source Code.
19."Distribution" means any of the following acts:
1. to transmit a work to a large number of specific persons through the Internet communication, broadcasting, and the like;
2. to transmit a work to the general public through the internet communication, broadcasting, and the like automatically in response to a request from the public; and
3. to distribute a copy of a work to the general public or a large number of specific persons.
Article 3. Copyright
1. The copyright of the Source Code shall be copied by Ken Saito.
Article 4. Licensee of Source Code
1. As provided for in this Article, I-lingu Iorum shall provide, and grant a license to use, the Source Codex fees of charge to any person who has taken the necessary procedure or registration as prescribed by I-lingu Iorum and agreed to his I-licens.
2. The Source Code shall be distributed exclusively by T-Engine Forum. Any person who obtains the Source Code under Article 4.1 above shall not make any re-Distribution of the Source Code.
3. In accordance with the license granted under Article 4.1 above, the Source Code User may perform the following acts:
1. to copy and/or modify the Source Code provided by T-Engine Forum hereunder for its own research, development and life.
2. to run the Source Code provided by I-Ingme forum hereunder for its own research, devellopment and the like.
3. to run the Source Code modified in accordance with the provision of Article 18 (1) above for its own research, development and the like.
4. to distribution the Hitory Code erated from the Source Codies prcised by 1980, Hureau Inducior or from the Source Codie madlred in accordance with the provision of Article 4-111 above.
4. In accordance with the license granted under Article 1.1 above, the System Developer may perform the following acts:
1. to perform any and all acts set forth In the Article 7.3 above.
2. to develop end manufacture the Embodied Product containing the Binyer Code, and, whether with or without payment, provide the End User with the same end made the Ehiary Code available to the End User on the Embodied Product.
5. The Source Code User and the System Developer shall be obligated to give an notice that the Source Code is used, in such a way as separately specified by TEngineer Forum when they use the Source Code or the Binary Code, or make the Binary Code available for the End User on the Embedded Product.
Article 5. Distribution of Modified Source Code
1. Any of a members of T-Engino Forum may become the Director of Misfitics by obtaining the approval of T-Engino Forum through the registration procedure as described by the Forum provided that only one of the members of the Committee which has been the registrant's procedure may distribute the information to any other member of the Board.
2. The Distributor of Modification may create the Modified Source Code based on the Source Code provided by T-Engine Forum and the Patch for Modification to be applied to create such Modified Source Code from the Source Code.
3. The Distributor of Modification shall prior to the distribution, inform T-Engine Forum of and register a name and description of the Modified Source Code in such way as specified by I-138 signature.
4. The Dator of Modification shall determine the name of the Modified Source Code subject to the rules separately established by TBS in Forum and put an appropriate notice as required by the rules on the Patch for Modification and the Modified Source Codes.
5. The Distributor of Modification may distribute the Modified Source Code to a third party, whether with or without payment, provided that the third parties or modification shall take the necessary measures to prohibit the third party from making his or her distribution of the Modified Source Code.
6. Developer with the Patch for Modification. Provided, however that the Distributor of Modification shall be obligated to confirm that the System Developer is the Source Code User duly licensed under Article 4.1.
7. The Distributor of Medication may perform the Vicarious Execution of Patient Processing or the System Developer.
8. The System Developer shall not distribute the Modified Source Code in further modified form to any third party as a stand alone, software product.
9. The System Developer may under the same obligation as invoked in Article 4.5, make the Embroider Project available or the End User through use of the Patch to Modification distributed by the Distributor of Modification or the Derivative Owners obtained through the Virious Fund of Force Processing.
Article 6. Distribution and Registration of the Ported Source Code
1. The Source Code User and the System Developer may whether with or without change, distribute to any third party only the following parts of the Porsed
Source Code on the Engine Hardware or the Similar Hardware to Engine Hardware:
1. The Hardware-dependent Part and Module-dependent Part, provided that the Source Code User and the System Developer shall inform T-FIGuro Forum of, and T-FIGuro Team's published, a method for distributing said Part to third parties.
2. The Leader File provided that the Leader File smal be distributed together with the Binary Code of the Ported Source Code.
2 Any member of T-Engine Forum may request T-Engine Forum to register and distribute, as an original source code for T-Channel, the Pared Source Code on the T Engine Hardware or the Similar Hardware to T Engine Hardware.
3 Any member of T Engne Forum who requests the distribution mentioned in the prooing cargraph shell assoe to the following conditions
1. The member shall confirm that the object hardware is the Engine Hardware or the Similar Hardware to Engine Hardware.
2. The member shall provide TEngine Forum with a complete set of operational environment for the object hardware and TKernel free of charge when requesting the distribution.
3. The member shall submit les results of the Pused Source Code to T-Engine Forum when requesting the distribution
4. In the event that I-Right's Forum accepts the required mention in Article 5.2, I-Right's Forum shall register and distribute the Honor Source Code as the Source Code for T-Kerner. Provided, however, that the Honor Source Code may be created in the same way as the Modified Source Code until the time of registrationendum.
6. The provison set forth in Article 3 shall apply to the Periodic Source Code registered in accordance with this Artice.
Article 7. Use for Other Purpose
1. Any use of this Source Code, no Modified Source Code or the Portod Source Code other than those stipulated in Articles 4, 5 and 6 shall be subject to the prior approval of T Pongo Forum.
Article 8. Limited Warranty
In Article 6.1 in the Parent's Copyright Code for any third party.
2. Ntioh t the r t h th t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t
3. 1994 1-1996 2005 1997 2008 2009 2010 2011 2012
Article 5. Indemnity
1. n t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t
Article 10. Breach of Agreement
1. In case that F-Engre Forum constitutes that this License Agreement is breached or that the population of - kernel to be included, F-Engre Forum shall take measures to correct such breach or such obstruction, lake measures on the ground of copyright infringement, or lake any other necessary measures against the breaching person or the obsercing person, regardless of whether or not, the said person is a member of F-Engre Forum.
2. In case of breach of this License Agreement by a member of T-Engine Forum, T-Engine Forum may take appropriate measures against the member; for example, the member is disqualified from membership, depending on what kind of breach has been committed by it.
3. Any legal dispute when any arise in relation to any process of this License Agreement shall be subject to the exclusive jurisdiction of the Tokyo 1st District Court
Article 11. Governing Law and Language
1. This License Agreement shall be governed by and interred under the laws of Japan.
2. This License Agreement is computed in both Japanese text and English text provisions than the Japanese text and govern the interpretation and performance of this License Agreement.
Apache License 2.0
Component Name License URL
mONsRspender conlour Apocia Licnrs 2.0http://www.apocia.org/ licenses/LCENSE-2.0
TERMS AND CONDITIONS FOR USE, REPRODUCTION, AND DISTRIBUTION
1.
Lcnsor shn the cnyght cner enity othcned by he copyright owner that is granting the lices.
A legal entity shall mean the union of the acting entity and a other officer that owns, manages or controls the property that is subject to such an action. The legal entity shall be defined as the organization which has the right to manage at least one, or more, of such action, whether by control or ownership, or by ownership of any part (50%) or more of the underlying states, or all beneficial ownership of such entity.
You ' re your eon n an oio o a h t h i t m f m
Oo: o: fo o o o o o o o o o o o o o o o o o o o o o o o o o o 0
Word mark means the work of authorship, whether in Source or Object form, made available under the License, as indicated by a copyright notice that is intended for or assigned to the work, an example is provided in the Appendix below.
Derivatives of Worsa shall mean any work, whether in Source of Otes form, is based on or derived from the work and/or work not considered necessary. Derivatives of Worsa shall be used to describe the work that is intended for use in the future. Derivatives of Worsa shall not include work that remains separate from, or merely link, them by nor to the interests of, the Wep and its derivatives Woter ware.
Contributions' shall mean any work of authorship, including the original version on the Work and any modifications or additions to Not Work or Derivative Works, thereof, that are necessarily submitted to Licensee for inclusion in the Work by the copyright owner or by an individual or Legal Entity authorized to submit on behalf of the copyright owner. For the purposes of the definition, "submitted" means all forms of electronic, webed, or written communication sent to the Licensee or its representatives, including but not limited to communication on electronic trading sites, source code control systems, and issue making systems which are managed by a third party. The term "copyright" is used to describe the use of the copyright owner's own communication from a company or organization or otherwise designated in writing as the copyright owner nor as "Not a Contributor." Contributors' shall mean Licensee and any individual or Legal Entity of whom a contribution has been received by Licensee and subsequently incorporated within the Work.
1. 2019. 3. 2018. 4. 2017. 5. 2016.
3. Grant of video license. Granted to this form and sanctioned by this license, each contributor hereby grants to You two perpetual, exclusive, non exclusive, no change, and no distribution rights for the use of this license. This license may not be used for advertising or promotional purposes. The use of such licenses applies only to those patent names which are associated with such contributor that are authorized by their copyright holder (a copy or by combination of their common ownership with the work to which such contributor was submitted.) You must publish your专利ightagreements any only (excluding a processor or counterfactual) in the form of a journal or otherwise published as a single journal or corporate patent infringement register, that any patent licenses granted to You will be the same as those for the work shall be included in all of the case such as the first one.
4. Fie t r f t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t
(ii You must give any other recipients of the Work or Derivate Works a copy of this License, and
b You Pst cale any mdded tis to carry proherl kies shing that You changed the Ties and
(1) you must retain, if the Source form of any Xerovites Writs does not display copyright, patent, trademark, and attribution notices from the Source form of the Writs, excluding these notices that do not pertain to any part of the Derivative Works; and
y the Nc t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t .
You may add Your own reply statement to Your modifications and may provide proofs of different license terms and conditions for use, reproduction, or distribution in other forms, or by any such use. Terms and conditions apply at the time of the work; otherwise written with a
and t t under the term and conditions of the License, without any additional terms or conditions. Nowhereading the above, nothing herein shall be reproduced or modified by any means without the prior written permission.
8. Trademarks. The Licensee does not grant permission to use the trade names, trademarks, or驰名商标, or product names of the Licensee except as required for reasonable customerry due in describing the origin of the Woro and reproducing the content of the NOTICE Note.
7. Declarer of tharity Unluee rresurbs to pucipat or sot in nong, dntion oce pror the wih hae cunl tio brols proie to comitng on an AISI BASE, WITHOUT FAVANTIES OF CONDITIONS OF ANY KIND, eithre expires or imdil, including the Writ and irimity, any wrtions or conditions of TILL, KONIN PRINSMENT, VURINE UNAIABILITY, OR FINISHES FOR A PARTICULAR PUPILS; You are solely responsible for deeming the appropriateness of using or redistributing the Writ and assunbllability associated with your Exceris of portions from this Iners
8. 1. Initiation of activity: In no secret and under no legal magic, whether in for (including nognoons), contract, or otherwise, unless required by applicable law (such as torts and rights) may be agreed to in writing, even by any controller to be liable to you for damages, including dry injury, sickness, special hidden or consequent damages of any shoulder arising as a result of this lease (except out of the use of invalidity). In use this resulting but not limited to damages for loss of use, such as computer failure or malfunction, or any act as well as commercial damages or losses, even if such controller has been advised of the possibility of such damages.
9. Accepting Authority or Additional Liabilities, While Subscribing the Work or Derivative Works (thereby), Your client chooses to offer and change a fee for acceptance of support, warrants Indemnity, or other facility obligations and/or rights consistent with this Licensee, in accepting such provision. Your clients may still cry on Your behalf and on Your side responsibility, not or shall be any other Contributor, and only If you agree to indemnity, extend, and hold each Contribution Terms and/or Facility throughout, or else as agreed upon, such Contributor or reason of your accepting any such authority or additional liability.
END OF TERMS AND CONDITIONS
APHINX: How to apply the Apoehn. Iossen to your work.
To apply the Apache License to your work, attach the following bottle plate code, with the fields enclosed by brackets "f" replaced with your own Identifying Information. The following details are provided for each license:
Copyright: yany [rare or copyright reserved]
Licensee over the Apache License, Version 2.0 (the "License"), your journal use this file except in compliance with the License. Your may obtain a copy of the License at http://www.apache.org/licenses/by/1.0/SN-1.0
Unk s t t t h t h t h t h t h t h t h t h t h t h t h t h t h t h t h t h t h t h t h t h t h t h t h t h t h t h t h t h t h t h t h t h t h t h t h t h t h t h t h t h t h t h t h t h t h t h t h t h t h t h t t a tht a
BZip2 License
This program, "bip2", the associated library "tabac", and all documents on the copyright (C) 1996-2007, Susan R. Seeward. All rights reserved.
Component Name License URL
http://2.0.8.Hopp/1976/2.prg
Herd distribution and use in source and binary forms, with or without modern on are permitted provided that the following conditions are met:
1. Ralribnions of sae rne cod must raer the anoe copyignt nore, this let of condtion and the folowing disdiames
2. The origin of the software must not be misrepresents, you must not claim that you wrote the original software. If you use the software in a product, an acknowledgement in this product documentation would not be produced but is required.
3. Altered source versions must be plainly marked as such, and must not be ininterpreteni as being the original software.
4. The name of the author may not be used to endorse or promote products derived from this Software without specify prior written permission. THIS SOFTWARE IS PROVIDED BY THE AUTHOR 'SAS' AND ANY EXPRESS OR IMPLIED WARTANS, INCLUDING BUT NOT LIMITED TO THE IMPLIED WARTANS OF MICHIGAN LIABILITY AND ALLS FOR A PAIR, CULIP ARTS OR DISCIPLINED IN, UNLESS OTHERWISE SHALL THE AUTHOR BE ALLOWED ANYTHING NEPTROPIC, INDIVIDUAL SPECIALL, EXAMPLIES OR COLORECTAL DARNINGS (INCLUDING, BUT NOT LIMITED TO) THE PROCESS OF SUBMIT USE OF SERVICES, USE OF DATA ON, TOGETO, OR BUSINESS INFORMATION, OVERSTATED AND USED AS THE BASIS OF THE USE OF DATA ON, TOGETO, OR BUSINESS INFORMATION, OR BOTH. THE USE OF DATA ON, TOGETO, OR BUSINESS INFORMATION, OR BOTH ARE NOT INCLUDED IN THE USE OF DATA ON.
JAN TOWR1 9eAaBbPzng
bipnep 105 of 12 Decmber 2007
University of Illinois / NCSA Open Source License
Copyright 1998-2007, The Board of Trustees of the University of Illinois All Rights Reserved.
Component Name License
Ier 2015 University of Hricle / NCSE Open Sources
perf performance test.
Mark Gates
Ary Thorne
Infergeruson
#
Feng Xin
Ken Cite
National Laboratory for Applied Networks Research
Natiior Center for SupercontpugAplicaion
Hysnly stlpoa at Lana Stampaan
HJ/12X40
Remn on h t o f the Software without limitation, including without limitation the rights to use, modify, marge, publish, distribute, sublntion, and/or sell copies of the software.
Redistribucne of source code must rete in the above coprph notice, this let of onnitone and the following deklaimes
Redribninc in riny fum must repudie the above copyright notice, the list of conditions and the following disainers in the documentation and other materials provided with the dicution.
The Nere of the n t f th r h t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t .
PHP 3.01 License
The PHP License, version 3.01 Copyright for 1998 - 2010 The PHP Group, All rights reserved.
Component Name License URL
p5.217F+F501http:/www.pprnstrributions
Redistribution and use in source and binary forms with or without modification is permitted provided that the following conditions are met:
1. Rddistribuions of source code must rear the above copyright noor, this list of cirditions and the following declared
2. Rclribations in binary form must reductre the above copyright rouse, this list of crlations and the following declaration in the documentation and or other materials provided with the copyright.
3. The name "HIP must be used to endorse or promote a product derived from this software without prior written permission. For written permission, choose contact group@ip.net
4. Products derived from this software may not be called "PHP", nor may "PHP" appear in their name, without prior writer permission from group@php.net. You may indicate that your software works in conjunction with PHP by saying "For or After" instead of calling it "PHP Foe" or "chptp".
5. The HPI Group may publish revised and/or new versions of the章程 from time to time such version will be given a disinguing version number. Once copies of the章程 has been published under a particular version or this form, you may always continue to use it under the form of this version. You may also choose to use such copies once under the terms of any subsequent version of this章程 published by the HPI Group. No one other than the HPI Group has the right to modify the term applicable to covered code created under the License.
6. Reriosions of any or whcse must elain the following aroodings: "This product includes PHP software, free, available from http://www. php-activations.com
THIS SOFTWARE IS PROVED BY THE PIP DEVELOPMENT TEAM ASGIS AND ANY EXPRESS OR IMPLIED WARRANTY, INCLUDING BUT NOT LIMITED TO, THE IMPLIED WARRANTY OF MERCHANTIBILITY AND FITNESS AND A PATTERCAL PURPOSE ARE DISCLOSED. IN NO EVENT SHALL THE PIP DEVELOPMENT TEAM OF ITS CONTINUING USE BEABLE FOR ANY DIRECT OR INDIRECT, INCIDENTAL, EXPLORATORY, CONVENTIONAL, MANUALS, NON-LOGICAL, OR ANYTHING OTHER THAN THE CONTRACT OR SERVICE OR WORK OR ACTIVITIES (A) AND ANYTHING ELSE THAN THE CONTRACT OR SERVICE OR WORK OR ACTIVITIES (B) AND ANYTHING ELSE THAN THE CONTRACT OR SERVICE OR WORK OR ACTIVITIES (C) AND ANYTHING ELSE THAN THE CONTRACT OR SERVICE OR WORK OR ACTIVITIES (D) AND ANYTHING ELSE THAN THE CONTRACT OR SERVICE OR WORK OR ACTIVITIES (E) AND ANYTHING ELSE THAN THE CONTRACT OR SERVICE OR WORK OR ACTIVITIES (F) AND ANYTHING ELSE THAN THE CONTRACT OR SERVICE OR WORK OR ACTIVITIES (G) AND ANYTHING ELSE THAN THE CONTRACT OR SERVICE OR WORK OR ACTIVITIES (H) AND ANYTHING ELSE THAN THE CONTRACT OR SERVICE OR WORK OR ACTIVITIES (I) AND ANYTHING ELSE THAN THE CONTRACT OR SERVICE OR WORK OR ACTIVITIES (J) AND ANYTHING ELSE THAN THE CONTRACT OR SERVICE OR WORK OR ACTIVITIES (K) AND ANYTHING ELSE THAN THE CONTRACT OR SERVICE OR WORK OR ACTIVITIES (L) AND ANYTHING ELSE THAN THE CONTRACT OR SERVICE OR WORK OR ACTIVITIES (M) AND ANYTHING ELSE THAN THE CONTRACT OR SERVICE OR WORK OR ACTIVITIES (N) AND ANYTHING ELSE THAN THE CONTRACT OR SERVICE OR WORK OR ACTIVITIES (O) AND ANYTHING ELSE THAN THE CONTRACT OR SERVICE OR WORK OR ACTIVITIES (P) AND ANYTHING ELSE THAN THE CONTRACT OR SERVICE OR WORK OR ACTIVITIES (Q) AND ANYTHING ELSE THAN THE CONTRACT OR SERVICE OR WORK OR ACTIVITIES (R) AND ANYTHING ELSE THAN THE CONTRACT OR SERVICE OR WORK OR ACTIVITIES (S) AND ANYTHING ELSE THAN THE CONTRACT OR SERVICE OR WORK OR ACTIVITIES (T) AND ANYTHING ELSE THAN THE CONTRACT OR SERVICE OR WORK OR ACTIVITIES (U) AND ANYTHING ELSE THAN THE CONTRACT OR SERVICE OR WORK OR ACTIVITIES (V) AND ANYTHING ELSE THAN THE CONTRACT OR SERVICE OR WORK OR ACTIVITIES (W) AND ANYTHING ELSE THAN THE CONTRACT OR SERVICE OR WORK OR ACTIVITIES (X) AND ANYTHING ELSE THAN THE CONTRACT OR SERVICE OR WORK OR ACTIVITIES (Y) AND ANYTHING ELSE THAN THE CONTRACT OR SERVICE OR WORK OR ACTIVITIES (Z) AND ANYTHING ELSE THAN THE CONTRACT OR SERVICE OR WORK OR ACTIVITIES (WZ) AND ANYTHING ELSE THAN THE CONTRACT OR SERVICE OR WORK OR ACTIVITIES (WZ) AND ANYTHING ELSE THAN THE CONTRACT OR SERVICE OR WORK OR ACTIVITIES (WZ) AND ANYTHING ELSE THAN THE CONTRACT OR SERVICE OR WORK OR ACTIVITIES (WZ) AND ANYTHING ELSE THAN THE CONTRACT OR SERVICE OR WORK OR ACTIVITIES (WZ) AND ANYTHING ELSE THAN THE CONTRACT OR SERVICE OR WORK OR ACTIVITIES (WZ) AND ANY THING OTHER THAN THIS SOFTWARE, EVEN IF MANDED BY THE POSSABILITY OF SLCH WAVE
The software corresits of voluntary contributions made by many individuals on behalf of the PHP Group. The PHP Group can be contacted via Email or group groups.
Rarmse fioomation on the HP Coup and the PHP project, ples see htp:/www.chipres. HP incldas the Zend Engne, frely available at: http://www zerd.com
zlib / libpng License
This software is provided as an in- without any means or implied warranty, in no way will the users be find liable for any damages arising from the use of this software.
Component Name License URL
2013/4/18 10:00 PM
Copyright (C) 1986-2010 Jean-Boue Gaffar and Mark Adler
Fer m t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t t
1. The origin of the software must not be misappropriated; you must not sioth that you wotte the original software if you use it as a software in a product, an appropriation in the product documentation would be appreciated but is not required.
2. Altered source versions must be pannly marked as such, and musl not be misrepresented as being the original software.
3. This notice may not be transmitted or otherwise from any source distribution.
see-boc Gaby Mark Apter
jogp@pogmber@alnnr.calees.com
The data normal used by the 210 tions is described by FI Cq (Frequen or Comming 1965 to 1982 in the Hes htp:/www.iongntic/1962010 (in formal), rno1661.tai palle format and rno162.aq: gao format).
Portions of this software are copyright 1998 The FrontType Project (www.fronttype.org). All rights reserved.

C
Toule réductrice entreprise dans la conception de ce nouvellement ne représentée par la participation responsable de la conformité pour annuler l'autorisation de l'utilisation à utiliser l'emploi.
Cé appellé est conforme au point 15 du réglement FCF. Son fonctionnement est souins aux deux conditions suivantes: (1) Cé appellé ne peut pas cause d'interférences mûblés et (2) Dàit accepté toute interférence reque, y compris les interférences susceptibles de cause un mauvais fonctionnement. Cé appellément a été testé et se conforme aux imèmes relatives à un apréciateur numérique de classe A conformant à la partie 15 des Réglementations FCF. Ces limites sont délabrés pour saufir un droit raisonnable du protection contre les interférences dangereuses si l'équiplement fonctionne dans un environnement commercial.
Céquipment généra, utilise et peut produit une énergie à radio fréquence, s'il est pas installé et utilisée selon le manuel d'instruction, il peut cause des inférieures nuisibles aux communications radiodionucléaires.
Le fonctionnement de cet équipement au sein d'une zone resténielle peut encouruer des interférences dangereuses, dans ce cas l'utilisation estromoed de corriger l'intérêrence avec ses propres frais.

Harwia Vision se socie de l'environnement à toutes les phases de fabrication du produit et s'engage à tout
mot en œuvre pour offrir à ses clients des produits plus respectieux de l'environnement.
La marque Eco represente l'engagement de Harwia Vision à creer des produits respectieux de l'environnement et
inclique que le produit est conformé à la Directive RoHS de l'Union europeenne.

Les bons gestes de mise au rebut de ce produit (Déchets d'équipements électriques et électroniques)
Applicable dans les pays de l'Union Européenne et dans d'autres pays européens pratiquant le tri sélectif.
Co symbolise sur la produit, ses accessoires ou sa documentation indicate que ni le produit, ni ses accessoires électroniques usages (chargeur, casque audio, cable USB, etc.) ne peuvent être liées avec les autres déchets menagers. La mise au début contrôlée des déchets presentaient des risques environnementaux et de sante publique, veillée séparer nos produits et accessoires usages des autres déchets. Vous favorissez ainsi le recyclage de la matière qui les compose dans le cadre d'un développement durable.
Les participaux sont invités à contacter le magazine leur ayant vendue le produit ou à se renseigner autres des autorisations locales pour contraitre les procédures et les points de colègue de ces produits en vue de leur recyclage. Les entreprises et professionnelles sont invites à contacter leurs fournisseurs et à consultier les conditions de leur contrat de vente. Ce produit et ses accessoires ne peuvent être joints avec les autres déchats professionnelles et commerciaux.

Elimination des batteries de ce produit
(Applicable au pays de l'Union Européenne et aux autres pays européens dans lesquels des systèmes de collecte selectively sont mis en place.)
Le symbole sur la batterie, manuel ou l'emballage indic que les batteries de ce produit ne doivent pas être éliminées en lin de vie avec les autres dichots morgans. L'indication éclicbile des socls chimiques Hg, Cd ou Pb signifie que la batterie content des quantités de meure, de cadmium ou de plomb supérieures aux niveaux de reference stipules dans la directive CE 2006/VEG. Si les batteries ne sont pas correctement éliminées, ces substances peuvent porter préclusifs à la santé humaine ou à l'environnement.
Ain de protet les resources naturelles et d'encourper la realitisation du materiel, veillez a securer les batteries des autres types de dcchets et a les recycler viaive son systeme local de collecte gratuite des batteries.

Hanwha
Vision
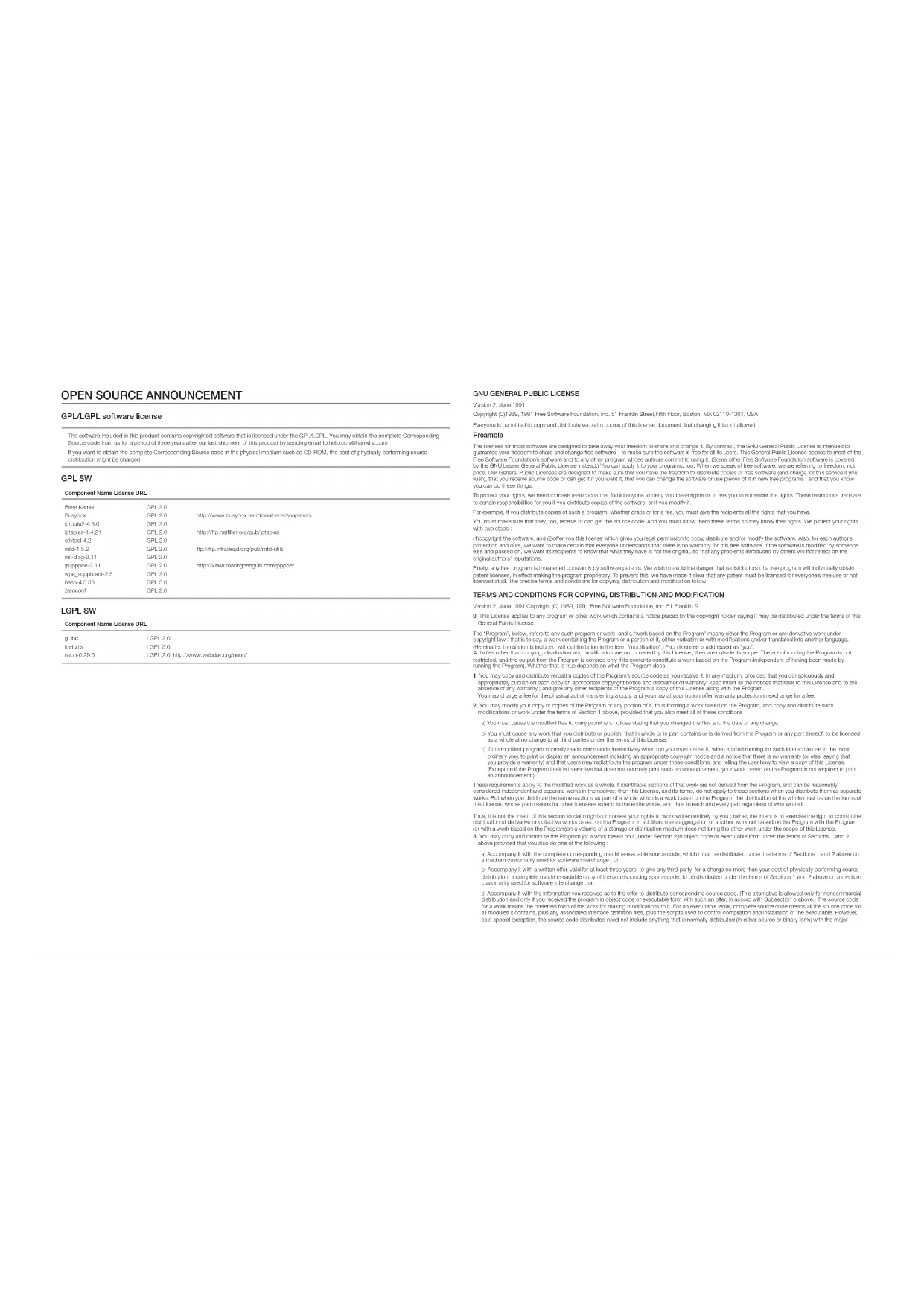
 EasyManual
EasyManual 




